North Korea's LABYRINTH CHOLLIMA Splinters into Three Specialized Cyber Units

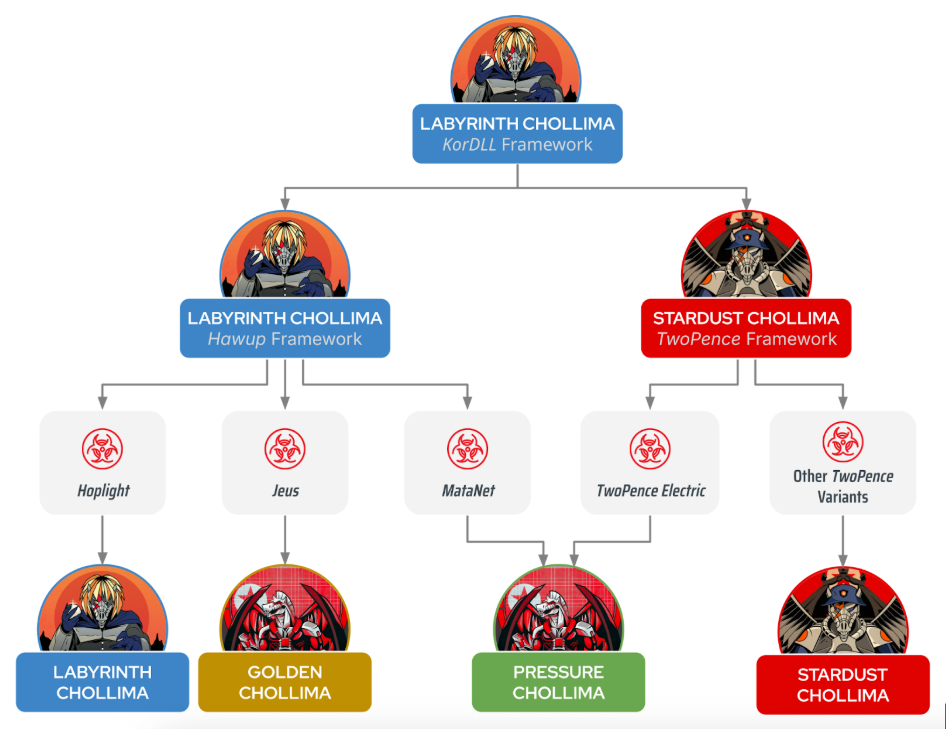
CrowdStrike Intelligence has reclassified LABYRINTH CHOLLIMA, the North Korean threat group behind the 2017 WannaCry ransomware attack, into three distinct operational units with specialized missions, malware, and targeting patterns.
The new attribution framework recognizes GOLDEN CHOLLIMA, PRESSURE CHOLLIMA, and a narrower core LABYRINTH CHOLLIMA group as separate adversaries that emerged between 2018-2020.
The Three Groups
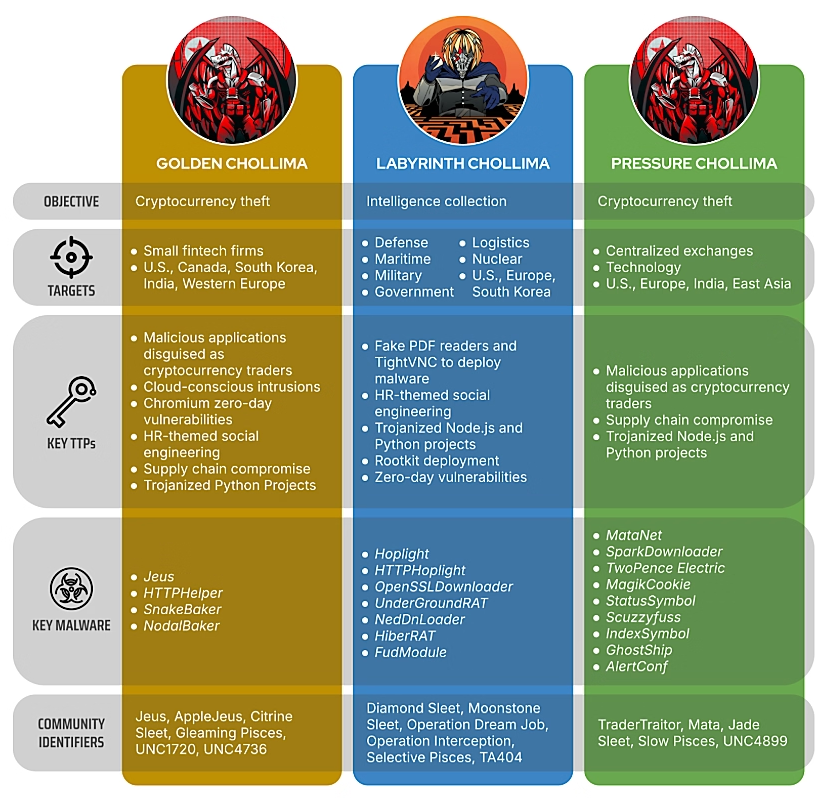
GOLDEN CHOLLIMA focuses on consistent, smaller-value cryptocurrency thefts targeting fintech and crypto entities in the U.S., Canada, South Korea, India, and Western Europe. The group likely provides baseline revenue generation for the North Korean regime.
Key capabilities include cloud-focused tradecraft, Chromium zero-day exploitation, and malware families like Jeus/AppleJeus, SnakeBaker, and NodalBaker. In late 2024, the group compromised a European fintech company through recruitment fraud, pivoted to cloud infrastructure, and diverted cryptocurrency to DPRK-controlled wallets.
PRESSURE CHOLLIMA conducts high-profile, high-value cryptocurrency heists regardless of geography—including the two largest cryptocurrency thefts on record. The group deploys sophisticated, low-prevalence implants and has evolved into one of the DPRK's most technically advanced adversaries.
LABYRINTH CHOLLIMA (core group) now focuses narrowly on espionage operations targeting manufacturing, defense, logistics, and critical infrastructure. Throughout 2024-2025, the group persistently targeted European aerospace corporations and defense manufacturers using employment-themed lures and zero-day exploits. Recent targeting includes logistics companies and U.S. critical infrastructure entities in specialized areas like hydroelectric power.
Shared Origins, Separate Missions
All three groups trace their lineage to the KorDLL malware framework (2009-2015), which spawned epoch-defining malware including Dozer, Brambul, Joanap, and eventually the Hawup framework used by modern LABYRINTH CHOLLIMA operations.
Despite operational separation, the groups share tools and infrastructure. FudModule, a rootkit employing direct kernel manipulation and zero-day exploits, has been observed in both LABYRINTH CHOLLIMA and GOLDEN CHOLLIMA operations—indicating centralized coordination within the DPRK cyber ecosystem.
Common Tradecraft
All three adversaries employ similar techniques reflecting their shared origins:
- Supply chain compromises
- HR and recruitment-themed social engineering
- Trojanized legitimate software
- Malicious Node.js and Python packages
- WhatsApp as an initial compromise vector
Why This Matters
The segmentation represents a strategic evolution allowing North Korea to simultaneously pursue revenue generation (GOLDEN and PRESSURE CHOLLIMA) and intelligence collection (core LABYRINTH CHOLLIMA). CrowdStrike assesses financial motivation will intensify as international sanctions continue, with the regime requiring funds for military projects including new destroyers, nuclear submarines, and reconnaissance satellites.
Targeted Sectors
| Group | Primary Targets |
|---|---|
| GOLDEN CHOLLIMA | Cryptocurrency, fintech |
| PRESSURE CHOLLIMA | High-value digital asset holders |
| LABYRINTH CHOLLIMA | Defense, aerospace, manufacturing, logistics |
Indicators of Compromise
Selected Malware Hashes (SHA-256):
LABYRINTH CHOLLIMA:
FudModule: cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b
Hoplight: 05feed9762bc46b47a7dc5c469add9f163c16df4ddaafe81983a628da5714461
Manuscrypt: dced1acbbe11db2b9e7ae44a617f3c12d6613a8188f6a1ece0451e4cd4205156PRESSURE CHOLLIMA:
Scuzzyfuss: b9f6a9d4f837f5b8a5dc9987a91ba44bc7ae7f39aa692b5b21dba460f935a0ae
SparkDownloader: 9ba02f8a985ec1a99ab7b78fa678f26c0273d91ae7cbe45b814e6775ec477598
TwoPence Electric: 081804b491c70bfa63ecdbe9fd4618d3570706ad8b71dba13e234069648e5e48GOLDEN CHOLLIMA:
Jeus: fe948451df90df80c8028b969bf89ecbf501401e7879805667c134080976ce2e
SnakeBaker: b6995c31a7ee88392fc25fd6d1a3a7975b3cb4ec3a9a318c3fcfaaf89eb65ce1
NodalBaker: 0518a163b90e7246a349440164d02d10f31d514a7e5cce842b6cf5b3a0cc1bfaRecommendations
- Train employees to recognize recruitment-themed social engineering, particularly via WhatsApp and unsolicited job offers
- Prohibit execution of software from untrusted sources
- Vet all third-party Node.js and Python dependencies before deployment
- Monitor cloud environments for unusual IAM enumeration or modification
- Implement multi-signature wallets and time-locked transfers for cryptocurrency operations
- Prioritize patching of RCE and SSRF vulnerabilities in public-facing applications



