Threats
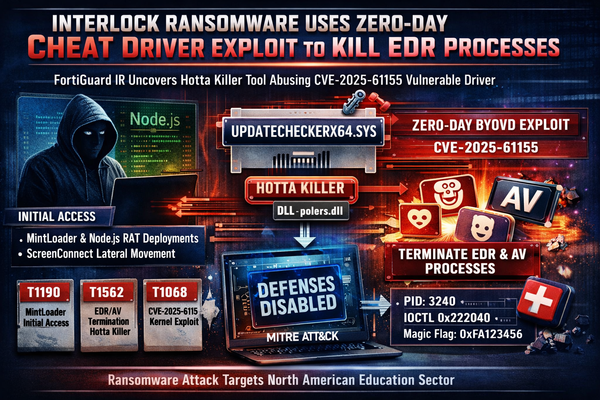
Interlock Ransomware Deploys Zero-Day Anti-Cheat Driver Exploit to Kill EDR Processes
FortiGuard Incident Response has documented a new tool in Interlock ransomware's arsenal — a bring-your-own-vulnerable-driver (BYOVD) process killer that abuses a zero-day vulnerability in a gaming anti-cheat kernel driver to terminate EDR and AV processes before ransomware deployment. The activity was observed during an intrusion against a North American