Pakistan-Linked APT Targets Indian Government with New Golang Malware Using GitHub for Command and Control
A Pakistan-linked advanced persistent threat group is targeting Indian government entities with three previously undocumented malware tools that leverage private GitHub repositories for command-and-control communication, according to research published by Zscaler ThreatLabz.
The campaign, dubbed Gopher Strike, deploys a new downloader called GOGITTER, a backdoor named GITSHELLPAD, and a shellcode loader called GOSHELL that ultimately delivers Cobalt Strike beacons to compromised systems. The attack chain demonstrates sophisticated targeting techniques including server-side checks that only deliver payloads to Windows systems with Indian IP addresses.
Spear-Phishing PDFs Initiate Attack Chain
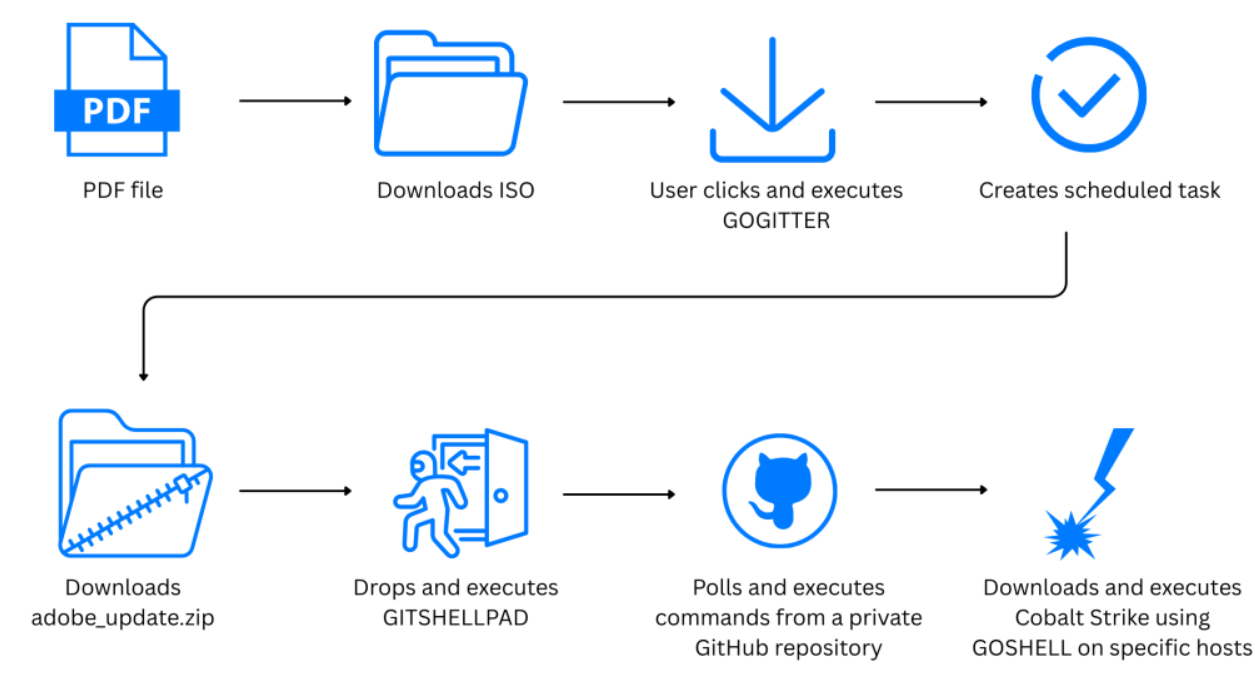
The campaign begins with spear-phishing emails containing PDF documents that display blurred images of legitimate government materials. The PDFs present a fake Adobe Acrobat update prompt with a "Download and Install" button to trick victims into downloading a malicious ISO file.
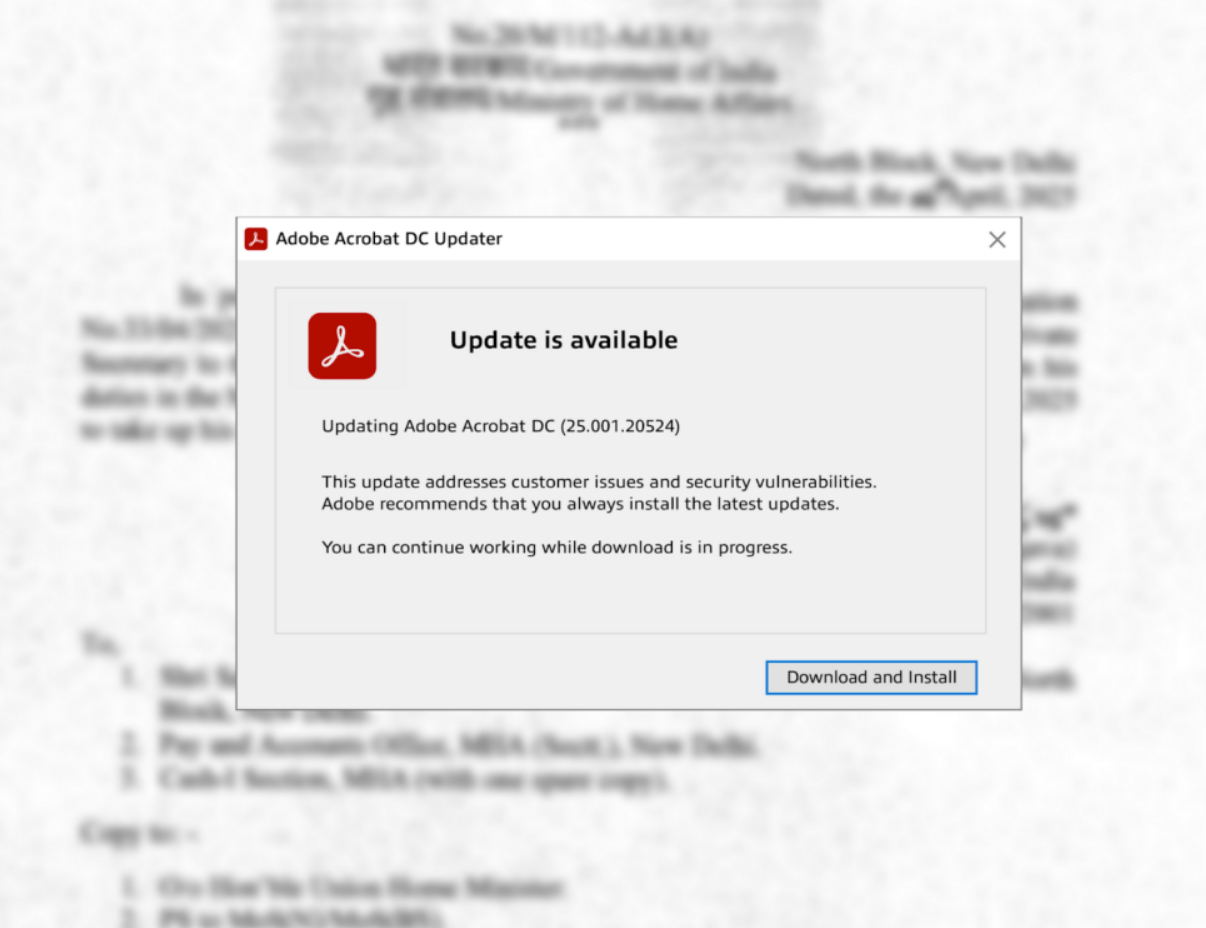
The payload delivery infrastructure implements geographic and platform filtering. Servers hosting the malicious files only respond with the ISO payload when requests originate from Indian IP addresses with User-Agent headers indicating Windows systems. These checks prevent automated analysis tools from retrieving the malicious files, ensuring delivery only to intended targets.
ThreatLabz identified multiple phishing PDFs used in the campaign with names referencing Indian government procedures including operational advisories, allowance circulars, and Ministry of External Affairs documentation.
GOGITTER Downloader Fetches Payloads from Private GitHub
GOGITTER is a lightweight 64-bit Golang-based downloader that serves as the initial stage of the infection chain. Upon execution, it drops a VBScript file named windows_api.vbs configured with two command-and-control URLs that fetch additional VBScript commands every 30 seconds.
The downloader establishes persistence by creating a scheduled task with a randomized name following the pattern MicrosoftEdge_ConfigurationUpdate_ followed by a four-digit number. This task executes the dropped VBScript every 50 minutes.
GOGITTER then downloads an archive named adobe_update.zip from a private threat actor-controlled GitHub repository using an authentication token embedded in the binary. The archive contains the GITSHELLPAD backdoor disguised as edgehost.exe.
GITSHELLPAD Backdoor Uses GitHub API for C2
GITSHELLPAD is a lightweight Golang-based backdoor that uses GitHub's REST API for bidirectional command-and-control communication. Upon execution, the backdoor registers victims by creating a new directory in the threat actor's private GitHub repository with the format SYSTEM- followed by the hostname, then adds an info.txt file containing Base64-encoded system information.
The backdoor polls the GitHub repository every 15 seconds for a command.txt file containing Base64-encoded instructions. Supported commands include changing directories, running commands in the background, uploading local files to the GitHub repository, downloading files to specified paths, and executing arbitrary commands via cmd.exe with output capture.
Command output and status messages are written to a result.txt file and uploaded to the threat actor's GitHub account. The command.txt file is deleted after successful execution to minimize forensic artifacts.
ThreatLabz discovered four threat actor-controlled private GitHub repositories and observed more than 200 post-compromise commands issued during the campaign. Commands included user and system reconnaissance using net user, whoami, and systeminfo, network configuration discovery, connectivity checks to C2 infrastructure, and downloading additional post-compromise tools.
GOSHELL Loader Deploys Cobalt Strike
After establishing access, the threat actors download RAR archives containing post-compromise tools including GOSHELL, a custom Golang-based shellcode loader used to deploy Cobalt Strike beacons.
GOSHELL implements multiple evasion techniques. The binary is artificially inflated to approximately one gigabyte by adding junk bytes to the PE overlay, likely to evade antivirus detection. The loader also implements environmental keying, only executing on specific hostnames by comparing the victim's hostname against a hardcoded list.
If the hostname matches, GOSHELL decodes an embedded second-stage shellcode using hex decoding and XOR operations with key 0xAA, sleeps for a random interval between three and seven seconds, then executes the shellcode using the QueueUserAPC API call.
The second-stage shellcode performs additional decryption using a four-byte XOR key to reveal the final payload, a stageless Cobalt Strike beacon configured to communicate over HTTPS with infrastructure hosted on CloudFront.
Attribution Assessment
While the campaigns share similarities with APT36, a known Pakistan-linked threat group, ThreatLabz assesses with medium confidence that the activity may originate from a new subgroup or another Pakistan-linked group operating in parallel.
The researchers note this analysis covers only the Gopher Strike campaign. A second campaign called Sheet Attack, which leverages Google Sheets, Firebase, and email for C2 communication, will be detailed in a forthcoming report that will also examine the use of generative AI in malware development.
Indicators of Compromise
Network indicators include the C2 domains govt-filesharing[.]site, ingov.myartsonline[.]com, workspace1.myartsonline[.]com, and adobe-acrobat[.]in. Payload hosting domains include adobereader-upgrade[.]in, adobecloud[.]site, and adobereader-update[.]in.
File indicators include multiple GITSHELLPAD samples with the filename edgehost.exe and phishing PDFs referencing Indian government circulars and advisories. The Cobalt Strike beacon communicates with d18c3nlvb0n2a6.cloudfront[.]net over HTTPS port 443.
Organizations in the Indian government sector should monitor for connections to private GitHub repositories from unexpected processes and investigate scheduled tasks with names mimicking Microsoft Edge updates.



