PDFSider Backdoor Deployed Against Fortune 100 Company Using DLL Side-Loading

A sophisticated Windows backdoor dubbed PDFSider has been identified in targeted attacks against enterprise environments, including a Fortune 100 financial services company.
The malware demonstrates APT-grade tradecraft while being deployed in ransomware operations, blending advanced evasion techniques with financially motivated attacks.
DLL Side-Loading via PDF24 Creator
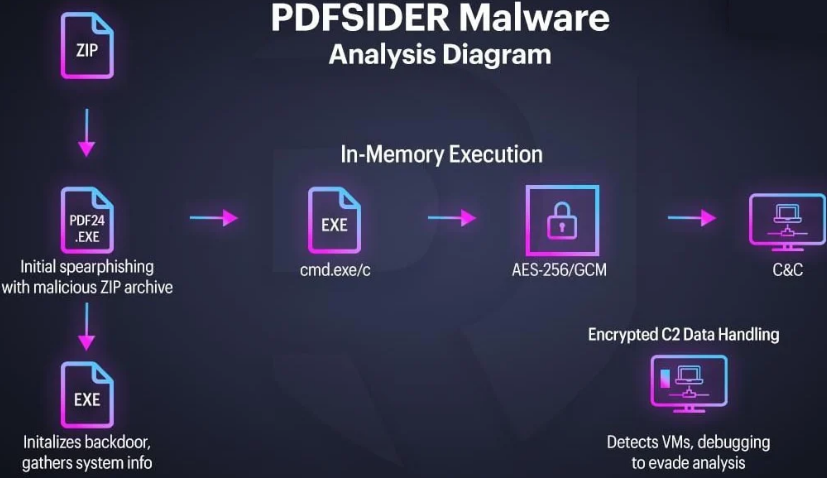
PDFSider is delivered through spearphishing emails containing ZIP archives with a legitimate PDF24 Creator executable bundled with a malicious DLL. The malware exploits DLL side-loading by masquerading as cryptbase.dll, a legitimate Windows system file.
When the trusted PDF24 executable runs, it loads the malicious DLL instead of the legitimate one, allowing the malware to execute within a signed, trusted process—effectively bypassing antivirus and EDR solutions.
Advanced Capabilities
The backdoor incorporates multiple sophisticated features:
- AES-256-GCM encrypted command-and-control communications
- DNS-based C2 channels to blend with normal traffic
- In-memory execution to avoid disk-based detection
- Anti-VM and sandbox evasion techniques
- System information exfiltration
- Persistence mechanisms for long-term access
Social Engineering Component
In the reported Fortune 100 incident, attackers combined PDFSider delivery with social engineering tactics. Victims received fake tech support calls requesting access via Microsoft QuickAssist, providing attackers with an initial foothold before deploying the backdoor.
Mitigations
Organizations should consider:
- Implementing application whitelisting and restricting DLL loading paths
- Monitoring or disabling remote access tools like QuickAssist in enterprise environments
- Training staff to recognize fake tech support social engineering
- Enforcing strict email attachment scanning policies
- Restricting execution of unsigned or unknown DLLs



