Researchers Uncover KazakRAT Campaign Targeting Central Asian Government Entities
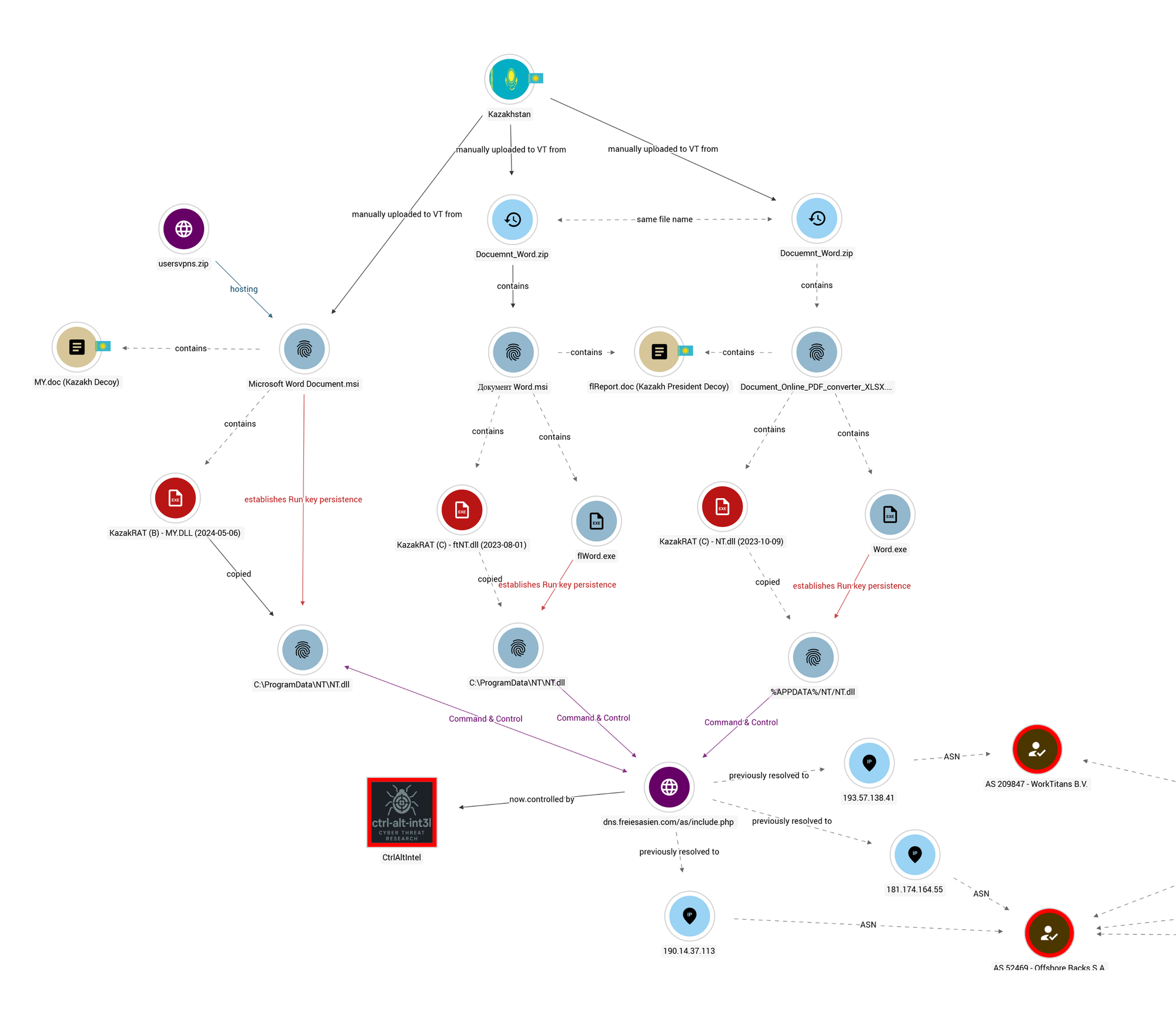
Security researchers at CtrlAltIntel have uncovered a persistent espionage campaign targeting government entities in Kazakhstan and Afghanistan using a previously undocumented Windows RAT they've dubbed KazakRAT. The campaign has operated since at least August 2022, with C2 infrastructure still active as of January 20, 2026.
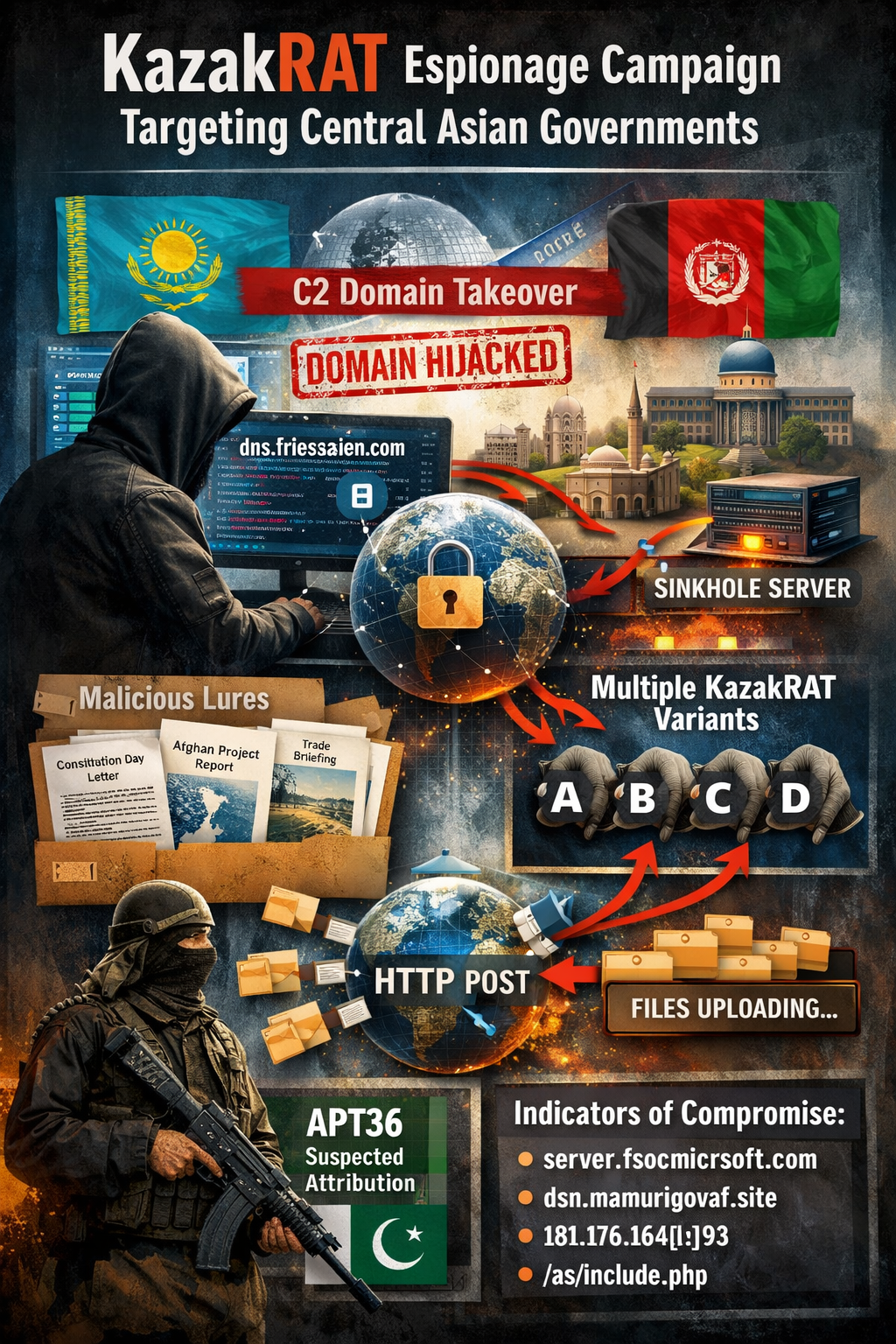
C2 Domain Takeover
In a rare operational win, researchers acquired one of the threat actor's expired C2 domains after the operators failed to renew it. By redirecting dns.freiesasien[.]com to a sinkhole, they confirmed active infections among Kazakh entities, with victim IP addresses still beaconing home from government and financial sector targets in the Karaganda region.
Delivery and Persistence
KazakRAT is delivered via malicious MSI installer files containing decoy documents tailored to victims. Observed lures include a fake letter from the President of Kazakhstan congratulating citizens on Constitution Day, official Afghan government correspondence about mosque construction projects, and economic briefings about foreign trade in the Karaganda region.
Regardless of variant, all samples persist via Windows Run registry keys, executing the RAT DLL through rundll32 at startup.
Technical Capabilities
The RAT communicates over unencrypted HTTP, beaconing to /as/include.php every five seconds for commands. Device IDs are derived from the victim's C: drive volume serial number.
Supported commands across variants include exec for running executables via CreateProcessW, disks for enumerating logical drives, info for host profiling and process enumeration, ctd for creating hidden directories, upload for downloading files to victim machines, and dir/aaa for file system enumeration. Exfiltration capabilities vary by variant, with commands dload, download, or dl used to steal files over HTTP POST.
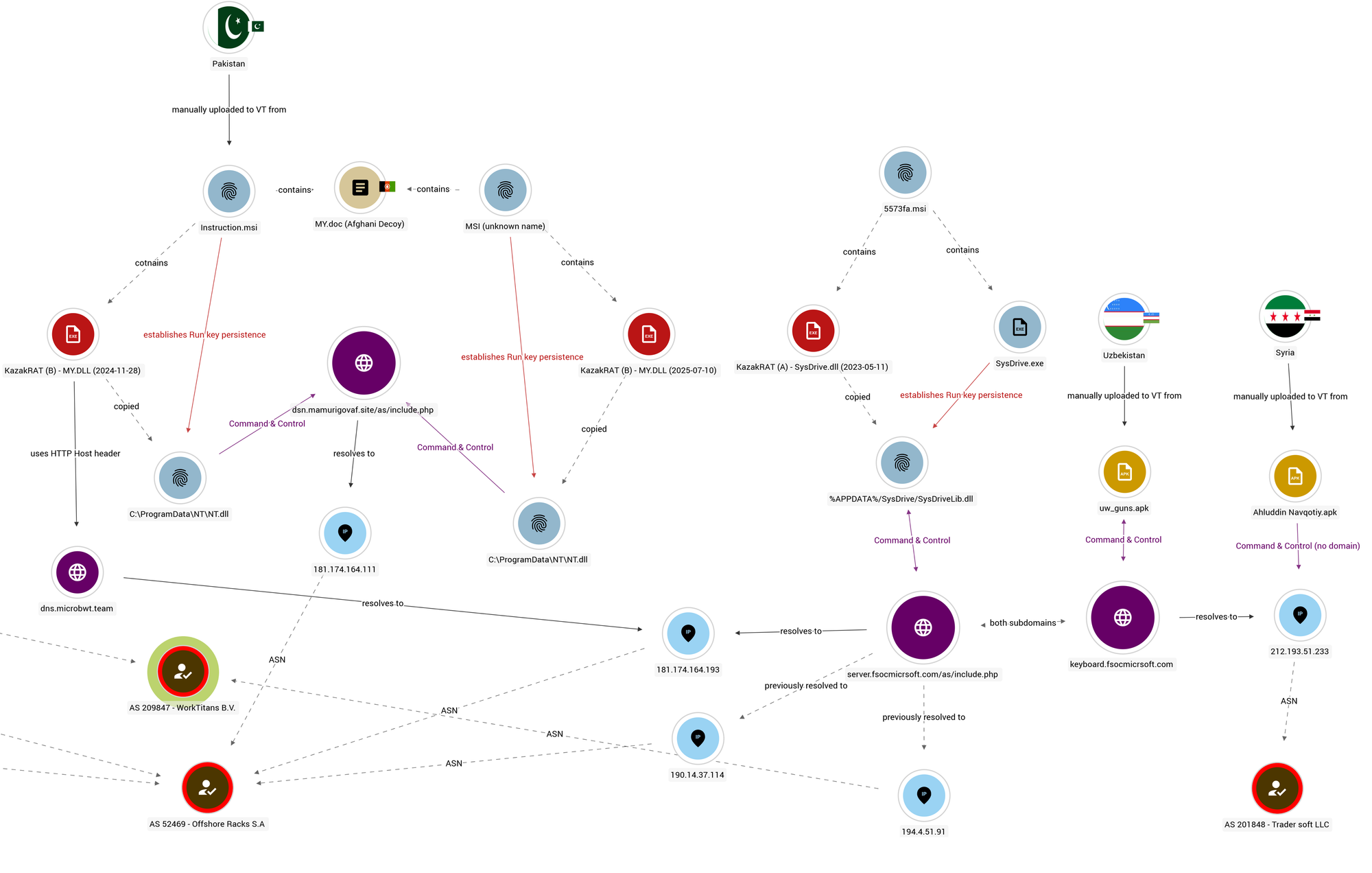
Multiple Variants
Researchers identified four KazakRAT variants (A through D) compiled between March 2023 and July 2025, indicating active development. The variants share core functionality with minor command-set differences. The malware is notably unobfuscated, suggesting limited emphasis on evasion.
Infrastructure
All observed C2 servers were hosted on two autonomous systems: AS209847 and AS52469. Active C2 domains include server.fsocmicrsoft[.]com, dsn.mamurigovaf[.]site, and dns.microbwt[.]team. One sample exhibited a mismatch between its configured C2 domain and HTTP Host header, suggesting possible infrastructure migration or operator error.
Attribution
While definitive attribution was not possible, researchers noted similarities to APT36 (Transparent Tribe), a Pakistan-linked group known for targeting Afghanistan, India, and Central Asia. Both groups employ modified versions of XploitSpy Android spyware and demonstrate persistent but relatively unsophisticated operational patterns.
The threat actor's use of overlapping infrastructure for both KazakRAT and XploitSpy campaigns targeting Uzbek and Syrian extremist groups suggests a broader regional intelligence collection mandate.
Indicators of Compromise
C2 domains: server.fsocmicrsoft[.]com, dns.freiesasien[.]com, dsn.mamurigovaf[.]site, dns.microbwt[.]team
Active C2 IPs: 181.174.164[.]193, 181.174.164[.]111
Beacon endpoint: /as/include.php (HTTP POST)
CtrlAltIntel has published YARA rules and full IOC lists for defender use.



