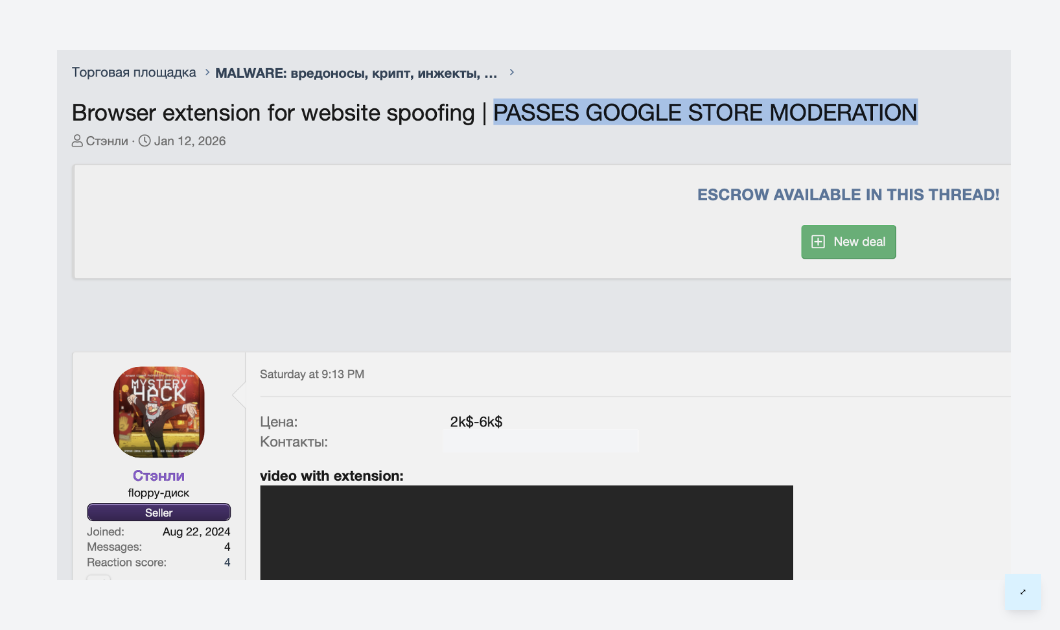
Russian Malware Toolkit Guarantees Chrome Web Store Approval for $6,000

A malware-as-a-service toolkit circulating on Russian cybercrime forums offers turnkey website spoofing capabilities disguised as a Chrome extension, with its premium tier guaranteeing publication on the official Chrome Web Store, according to research published by Varonis.
The toolkit, dubbed Stanley after the seller's alias, sells for $2,000 to $6,000 and enables attackers to display phishing pages while the browser's URL bar shows the legitimate domain. Varonis reported the threat to Google and the hosting provider on January 21, 2026. The command-and-control server was taken offline the following day, but the extension remains live on the Chrome Web Store.
Browser Attacks Escalating Rapidly
The discovery comes amid an unprecedented surge in browser-based attacks. In December 2025, a campaign called DarkSpectre compromised 8.8 million Chrome, Edge, and Firefox users through three linked operations, exposing fundamental gaps in browser security.
January 2026 brought additional concerns when two extensions with a combined 900,000 installations were caught quietly siphoning ChatGPT and DeepSeek conversations. One of the malicious extensions carried Google's "Featured" badge, indicating it had passed enhanced review processes.
Around the same time, the CrashFix campaign manipulated users into installing a remote access trojan by intentionally crashing their browsers and posing as the solution to the problem it created.
Chrome Web Store Guarantee Is the Selling Point
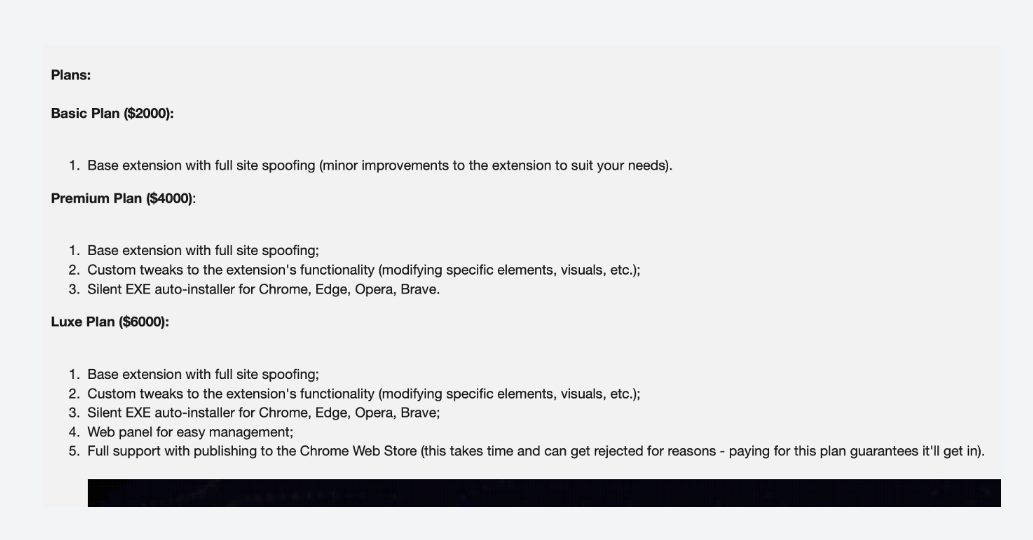
Stanley first appeared on January 12, 2026, promoted with explicit claims that the extension "passes Google Store moderation." The seller pairs the listing with feature demonstrations and video showing the spoofing workflow against Binance and Coinbase cryptocurrency exchanges.
The pricing structure places the Chrome Web Store publication guarantee at the commercial center of the offering. The top tier bundles customization, a management panel, and assured approval through Google's review process, shifting distribution risk away from buyers and implying the seller has a repeatable method for clearing moderation.
The extension masquerades as "Notely," a minimalist note-taking and bookmarking tool. The legitimate functionality serves dual purposes: it provides plausible cover for the extensive permissions required, and it helps the extension accumulate positive reviews before malicious functionality is activated.
Full Website Spoofing Capability
The toolkit's core capability enables complete website spoofing while keeping the browser's address bar intact. When a victim navigates to a targeted website, the extension intercepts the navigation and overlays a fullscreen iframe containing the attacker's phishing page.
The browser's URL bar continues displaying the legitimate domain while the victim sees and interacts entirely with attacker-controlled content. Demonstration videos show binance.com displayed in the address bar while the page content is completely controlled by the attacker.
The management panel provides operators with a web-based interface displaying all infected users by IP address, online status, last activity timestamp, and browser history. Operators can select individual infections for targeted actions and configure URL hijacking rules per victim, setting source URLs for legitimate sites to hijack and target URLs for phishing pages to display.
Rules can be activated or deactivated per infection, allowing operators to stage attacks and trigger them on demand. A simple dialog accepts any source and target URL pair, making configuration trivial.
Push Notifications Add Active Attack Vector
Beyond passive hijacking, operators can actively lure victims to targeted pages through real-time Chrome notification delivery. Because the notifications originate from Chrome itself rather than a website, they carry implicit trust with users.
Demonstration materials show generic messages like "new bookmark available," but operators can customize notification text and pair it with any redirect URL, enabling targeted social engineering at scale.
Technical Implementation
Analysis of a sample extension reveals the permissions grant complete control over every website the victim visits. The extension requests access to tabs, web navigation, storage, notifications, and scripting capabilities across all URLs. Content scripts inject at document start, ensuring malicious code executes before any page content loads.
The extension uses victim IP addresses as unique tracking identifiers rather than generating random IDs. This enables attackers to target specific individuals, correlate users across multiple browsers and devices, and implement geographic targeting for region-specific phishing campaigns.
A persistent polling mechanism checks in with the command-and-control server every 10 seconds, receiving URL hijacking instructions and confirming attack delivery. The toolkit implements backup domain rotation, automatically cycling through fallback domains if the primary C2 is taken down to maintain operational continuity.
Code Quality Suggests Value Is in Access
Varonis researchers noted the implementation is functional rather than sophisticated. The techniques including iframe overlay, header stripping, and C2 polling are well-documented, and the code contains rough edges including Russian-language comments, empty catch blocks, and inconsistent error handling.
The $6,000 price tag likely reflects the value of the Chrome Web Store publication guarantee and management panel rather than code complexity. The guarantee represents the real commercial value, providing buyers with distribution through a trusted channel that most users consider safe.
Enterprise and Consumer Defenses
The publication guarantee undermines standard security advice about installing only from official stores and checking reviews. Malicious extensions that pass Google's review process can remain active for months before detection, harvesting credentials from thousands of users.
For enterprises, Varonis recommends strict extension allowlisting through Chrome Enterprise or Edge for Business, blocking all extensions except those explicitly approved. This requires overhead for maintaining approved lists and evaluating requests but prevents threats that slip past store moderation.
For consumers, the researchers advise periodic audits of installed extensions, removing anything not actively used. Permission requests warrant scrutiny, particularly extensions asking for access to all websites or browsing history. Fewer extensions means smaller attack surface.
Architectural Problem Enables Ongoing Abuse
The deeper issue is architectural. Browser extension marketplaces use a review-once, update-anytime model, allowing extensions to pass review as legitimate tools and push malicious updates later. Until that model changes, toolkits like Stanley will continue slipping through moderation.
BYOD policies, SaaS-first environments, and remote work have made the browser the new endpoint, and attackers have taken notice. Malicious browser extensions have become a primary attack vector accessible to everyone from solo scammers to organized crime groups.
Indicators of Compromise
The threat actor operates under the forum alias Стэнли. Network indicators include the C2 domain api.notely.fun, login panel at notely.fun/login, and IP address 72.61.83.67. The malicious extension uses ID AKELIEKMEAIFANBDFKNJOELHMMEBLGGH and presents as Notely version 1.0.



