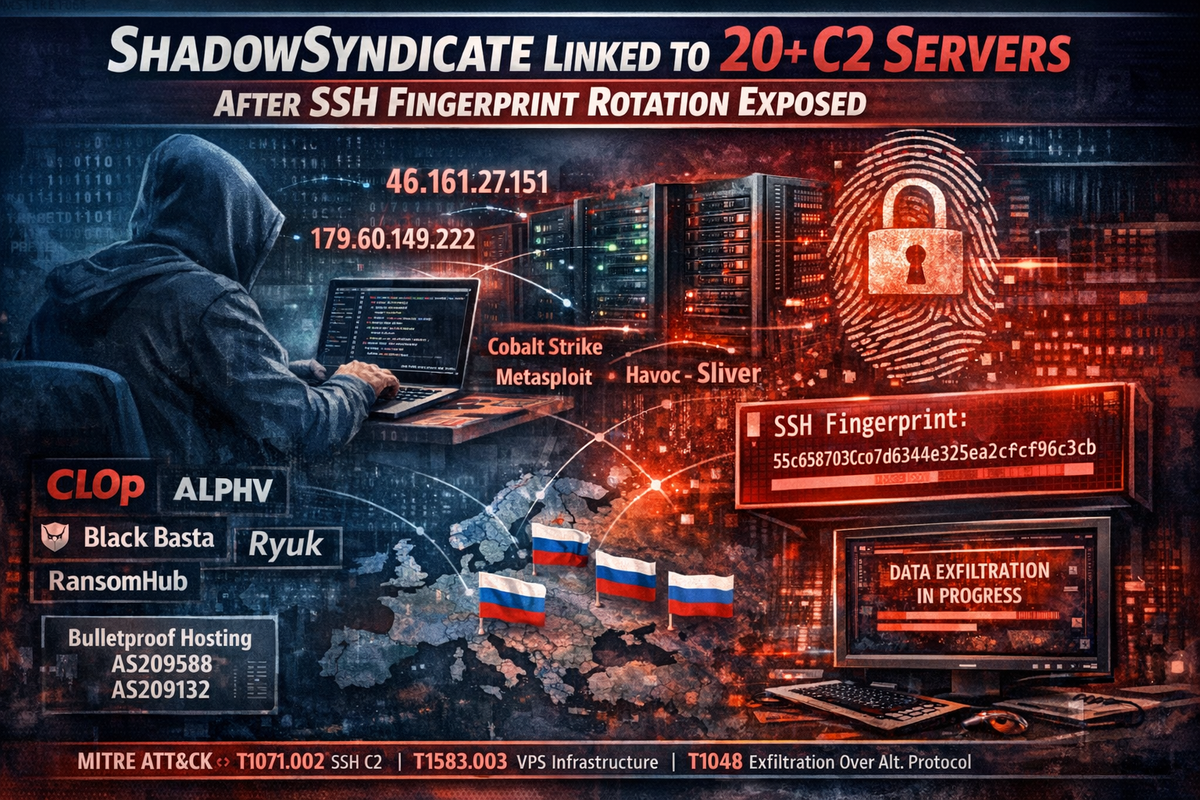
ShadowSyndicate Linked to 20+ C2 Servers After SSH Fingerprint Rotation Technique Exposed
ShadowSyndicate, a cybercrime cluster first identified in 2023, has been caught using a server transition technique designed to obscure operational continuity across its infrastructure — but OPSEC failures have given researchers visibility into the group's C2 network.

Group-IB confirmed two additional SSH fingerprints linked to ShadowSyndicate operations in February 2026. Overlapping SSH key presence on shared servers exposed the connections, revealing at least 20 servers functioning as command-and-control infrastructure for Cobalt Strike, Metasploit, Havoc, Mythic, and Sliver attack frameworks.
The technique works by rotating SSH fingerprints across server clusters to mimic legitimate ownership transfers. When executed cleanly, each rotation creates plausible deniability between previous and current operators. ShadowSyndicate failed to fully separate key material during transitions, leaving overlapping fingerprints that linked the clusters together.
Ransomware Connections
The infrastructure maintains confirmed associations with Cl0p/Truebot, ALPHV/BlackCat, Black Basta, Ryuk, and Malsmoke campaigns. During RansomHub intrusions investigated between September and October 2024, Darktrace observed data exfiltration to ShadowSyndicate-associated servers via SSH, with 46.161.27[.]151 specifically identified as C2 infrastructure.
Researchers assess ShadowSyndicate likely operates as either an Initial Access Broker or bulletproof hosting provider — potentially both. MeshAgent remote management tooling was observed on 179.60.149[.]222 alongside SSH fingerprint 55c658703c07d6344e325ea26cf96c3b, suggesting hands-on-keyboard access to compromised environments.
Infrastructure Patterns
The group shows consistent preference for specific European bulletproof hosting providers that disguise operations as VPN or proxy services using layered autonomous system numbers including AS209588 and AS209132. Security analysts assess with moderate confidence that these providers operate from Russia through offshore shell entities.
Despite rotating credentials and server ownership, ShadowSyndicate's repeated reliance on the same ASNs and hosting providers creates predictable attribution patterns that enable proactive detection through infrastructure correlation.
The infrastructure remains active as of February 2026, continuing to scan for vulnerabilities and deploy payloads.
Indicators of Compromise
- 46.161.27[.]151 (C2 — linked to RansomHub data exfiltration)
- 179.60.149[.]222 (MeshAgent deployment)
- SSH fingerprint: 55c658703c07d6344e325ea26cf96c3b
- AS209588, AS209132 (bulletproof hosting infrastructure)
MITRE ATT&CK: T1071.002 (Application Layer Protocol: SSH), T1583.003 (Acquire Infrastructure: Virtual Private Server), T1588.001 (Obtain Capabilities: Malware), T1048 (Exfiltration Over Alternative Protocol), T1219 (Remote Access Software)



