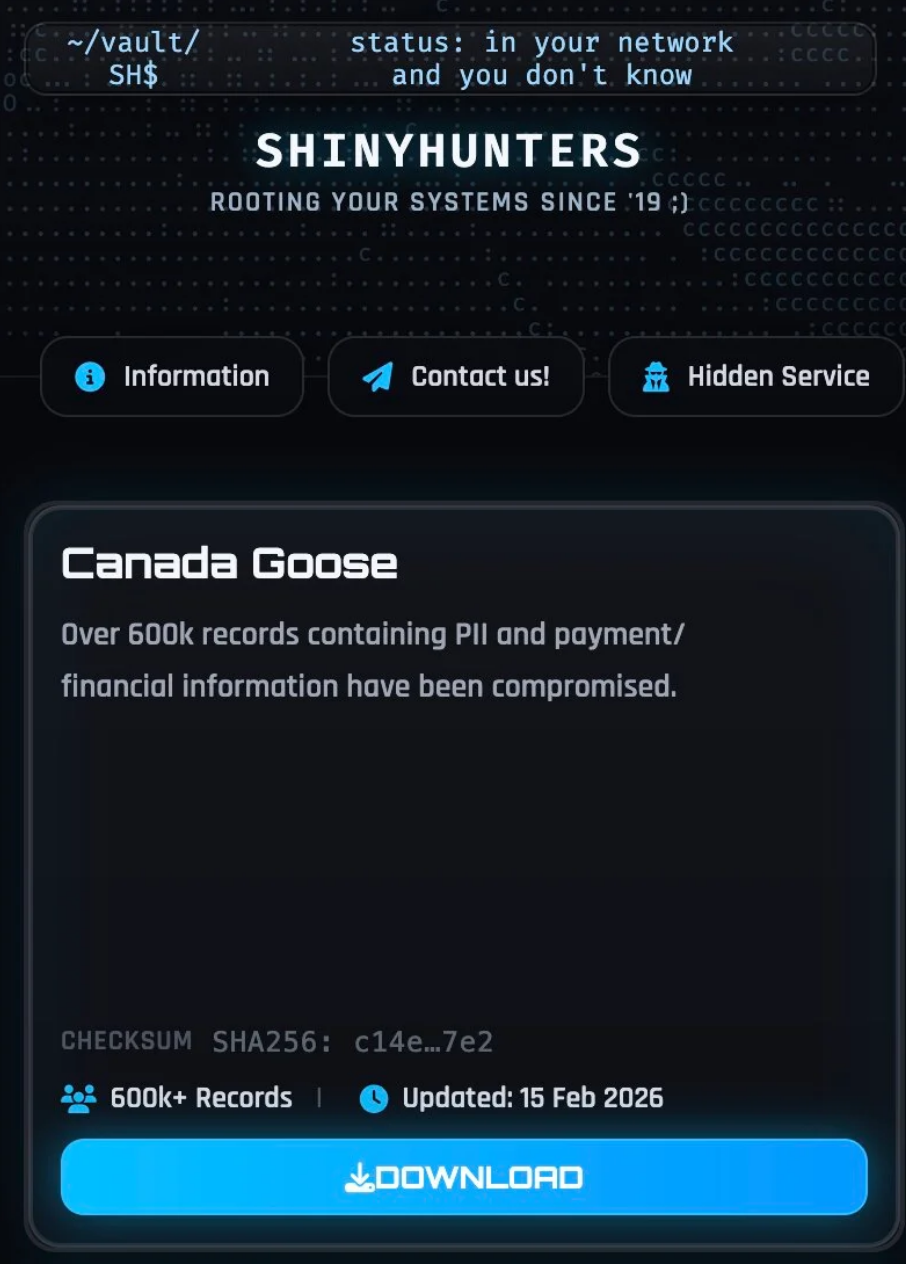
ShinyHunters Claims 600,000 Customer Records From Canada Goose as Third-Party Payment Processor Breach

Data extortion group ShinyHunters has published over 600,000 customer records from Canadian luxury outerwear brand Canada Goose, including personal information, partial payment card data, and detailed e-commerce order histories.
Canada Goose, a Toronto-based brand founded in 1957 with a global retail footprint and nearly 4,000 employees, confirmed awareness of the leak but said it has found no evidence of a direct breach of its own systems.
1.67 GB Dataset
The 1.67 GB dataset, released in JSON format on ShinyHunters' data leak site, contains detailed e-commerce order records including customer names, email addresses, phone numbers, billing and shipping addresses, IP addresses, and full order histories.
Partial payment card information is also present — card brand, last four digits, and in some cases the first six digits (BIN) — along with payment authorization metadata. Full card numbers do not appear to be included.
The records also contain purchase history, device and browser fingerprinting data, and order values, providing enough detail for attackers to profile high-value customers for targeted phishing and social engineering.
Third-Party Origin Claimed
When asked whether the data originated from ShinyHunters' recent wave of SSO and cloud-targeting attacks, the group told BleepingComputer the dataset was unrelated, claiming it came from a third-party payment processor breach dating back to August 2025.
The dataset's schema supports this claim — field names like checkout_id, shipping_lines, cart_token, and cancel_reason closely resemble e-commerce checkout exports commonly associated with hosted storefront and payment processing platforms rather than a direct compromise of Canada Goose's own infrastructure.
ShinyHunters Continues Escalation
This is the latest in an accelerating series of incidents linked to ShinyHunters, one of the most prolific data extortion groups currently operating. The group has recently been tied to vishing and social-engineering campaigns targeting corporate SSO accounts and cloud environments, and claimed a second member was arrested in early February as its infrastructure came under increased law enforcement pressure.
Despite these disruptions, the Canada Goose leak demonstrates ShinyHunters remains operationally active and continues publishing stolen datasets when victims refuse to pay.
Recommendation
Canada Goose customers should monitor for targeted phishing attempts leveraging the exposed personal and transaction data. The combination of names, addresses, phone numbers, partial payment data, and purchase history provides ample material for convincing social engineering. Customers who made purchases through Canada Goose's e-commerce platform should verify financial statements, be cautious of communications referencing specific past orders, and avoid clicking links in unsolicited messages claiming to be from the brand.



