ShinyHunters Claims Second Leader Arrested as Group's X Account Suspended

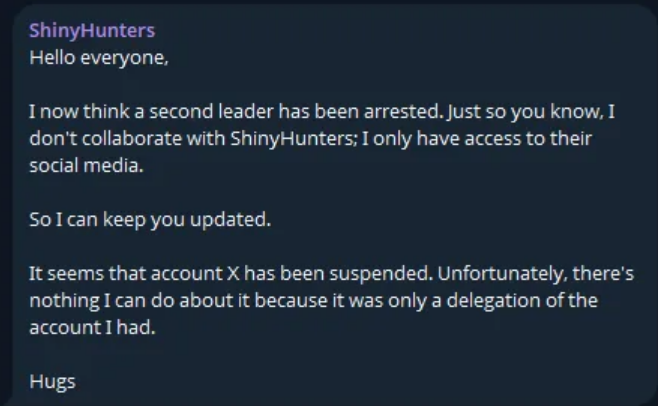
ShinyHunters, one of the most prolific data breach and extortion groups of the past five years, has posted a message to their official Telegram channel claiming that a "second leader has been arrested."
The brief update also confirmed that the group's X (formerly Twitter) account has been suspended and cannot be recovered.
No additional details were provided regarding the identity of the arrested individual, the jurisdiction involved, or the circumstances of the arrest.
Background
ShinyHunters first emerged in 2020 and quickly became one of the most active data breach actors in the cybercriminal ecosystem. The group is responsible for breaching dozens of major organizations, including Ticketmaster, AT&T, Microsoft, Tokopedia, Wishbone, and Mashable — collectively exposing hundreds of millions of user records.
In July 2024, French authorities arrested Sebastien Raoult, a 22-year-old French national extradited from Morocco, who pleaded guilty to charges related to ShinyHunters operations. Raoult was sentenced to three years in federal prison and ordered to pay over $5 million in restitution.
If confirmed, today's claim of a second leadership arrest would mark another significant blow to the group's operational capability.
Implications
The combination of leadership arrests and platform deplatforming suggests mounting pressure on ShinyHunters' ability to operate openly. However, the group has historically demonstrated resilience — pivoting between communication channels, marketplaces, and operational models.
Organizations previously targeted by ShinyHunters or operating in sectors the group has historically focused on — SaaS platforms, technology companies, gaming, and e-commerce — should remain vigilant for potential retaliatory leaks or opportunistic attacks by remaining group members.



