ShinyHunters Escalates SaaS Data Theft with Vishing and MFA Manipulation
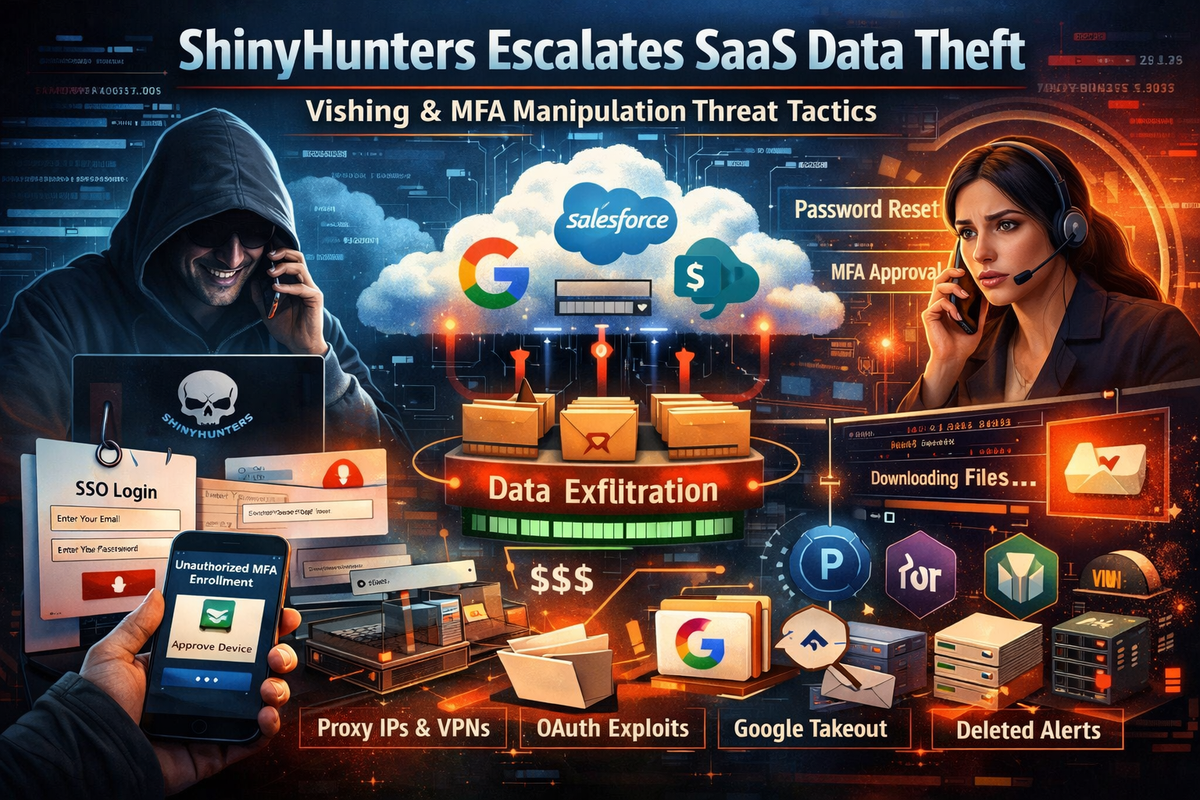
Mandiant has published a detailed analysis of an escalation in threat activity linked to ShinyHunters-branded extortion operations. The campaigns leverage evolved voice phishing (vishing) techniques and victim-branded credential harvesting pages to compromise single sign-on credentials and enroll unauthorized devices into victim MFA solutions — enabling access to cloud SaaS environments for large-scale data theft.
Critically, this activity does not exploit any product vulnerability. These intrusions succeed entirely through social engineering, targeting human-driven workflows like help desk password resets, MFA enrollments, and device registrations.
How the Attacks Work
The ShinyHunters-affiliated clusters are using a consistent playbook: vish help desk staff or end users into resetting credentials or enrolling attacker-controlled devices into MFA, then pivot from the compromised SSO provider (typically Okta or Entra ID) into downstream SaaS platforms including Google Workspace, Salesforce, SharePoint, Atlassian, and DocuSign.
Once inside, the threat actors abuse native SaaS capabilities for exfiltration — Google Takeout exports, PowerShell-driven SharePoint downloads, Salesforce Data Loader, and bulk report exports. They also clean up evidence by deleting security notification emails (e.g., "Security method enrolled" or "new sign-in" alerts) from victim mailboxes.
Mandiant emphasizes that attackers are specifically targeting non-human identities (service accounts, API keys, OAuth tokens) due to limited detections around these, lack of behavioral baselines, and the privileged roles commonly assigned to them.
Immediate Containment Priorities
For organizations responding to an active or suspected intrusion, Mandiant recommends:
- Revoke active sessions — Disable compromised accounts and revoke all session tokens and OAuth authorizations across IdP and SaaS platforms
- Restrict password resets — Temporarily disable self-service password reset portals, especially for administrative accounts
- Pause MFA registration — Block all new device enrollments at the IdP level
- Limit remote access — Restrict or disable VPN/VDI ingress from untrusted or non-compliant devices
- Enforce device compliance — Lock authentication to managed, compliant devices and known egress locations
- Implement shields-up procedures — Shift to manual, high-assurance verification for all account-related requests; remind staff not to accept work direction via SMS
During containment, all password and MFA resets should be routed through rigorous manual identity verification — Mandiant specifically recommends live video verification where the user holds a government ID next to their face, with out-of-band manager approval required.
Long-Term Hardening
Mandiant's hardening recommendations center on three pillars:
Phishing-Resistant MFA: Remove SMS, phone, push, and email as authentication methods. Deploy FIDO2 security keys or passkeys. Enforce multi-context criteria (device + location + identity) for authentication transactions.
Identity & Access Management: Restrict access to managed devices only. Limit local accounts in SaaS platforms. Reduce scope of non-human accounts, centralize secrets in a manager, restrict authentication IPs for programmatic credentials, and transition to workload identity federation with short-lived tokens.
Platform-Specific Controls:
- Okta — Enable ThreatInsight, restrict Super Admin to corporate VPN network zones
- Entra ID — Implement Conditional Access Policies, risk-based policies, restrict application registration
- Google Workspace — Use Context-Aware Access, enforce 2SV, enable Advanced Protection for high-risk users
- AWS — Apply SCPs to limit attack surface, define data perimeters via RCPs, alert on GetCallerIdentity from non-corporate IPs
- Azure — Enforce CAPs requiring hybrid-joined compliant devices, implement JIT via PIM, use Managed Identities
- GCP — Configure VPC Service Controls, enforce org policies like
iam.disableServiceAccountKeyCreation, apply IAM Conditions to sensitive bindings
Detection Playbook
Mandiant provides YARA-L pseudo-code detection rules targeting the behavioral patterns observed in these intrusions. Key detections include:
MFA Lifecycle Monitoring — Alert on MFA enrollment, activation, deactivation, or reset events, especially when correlated with recent password resets or sign-in anomalies within a 30-minute window.
Suspicious Admin Actions from Anonymized IPs — Flag Okta admin/security policy changes originating from VPN, proxy, or Tor ASNs.
OAuth App Authorizations — Detect authorization of known attacker tools like ToogleBox or "recall" OAuth apps in Google Workspace that enable mailbox manipulation.
Security Notification Deletion — Alert on Gmail or Exchange deletion of emails with subjects matching MFA enrollment, new sign-in, or security verification patterns.
Google Takeout Exports — Detect Takeout export initiation and completion events, especially exports exceeding 500MB from non-approved users.
PowerShell SharePoint Downloads — Flag FileDownloaded events with PowerShell user-agent strings, particularly when burst volume exceeds 20 downloads or 500MB in a 15-minute window.
Cross-SaaS Auth from Campaign Infrastructure — Detect authentication attempts across SSO/SaaS platforms originating from known ShinyHunters proxy IPs or flagged VPN/Tor ASNs.
Off-Hours Identity Activity — Alert on password resets, MFA enrollments, or device registrations occurring outside normal business hours.
Multi-User MFA Enrollment from Single IP — Detect the same source IP enrolling MFA for 3+ distinct users within 10 minutes, indicating help desk manipulation.
Credential Harvesting Domain Detection — Flag DNS queries or HTTP requests matching brand + SSO keyword lookalike domains.
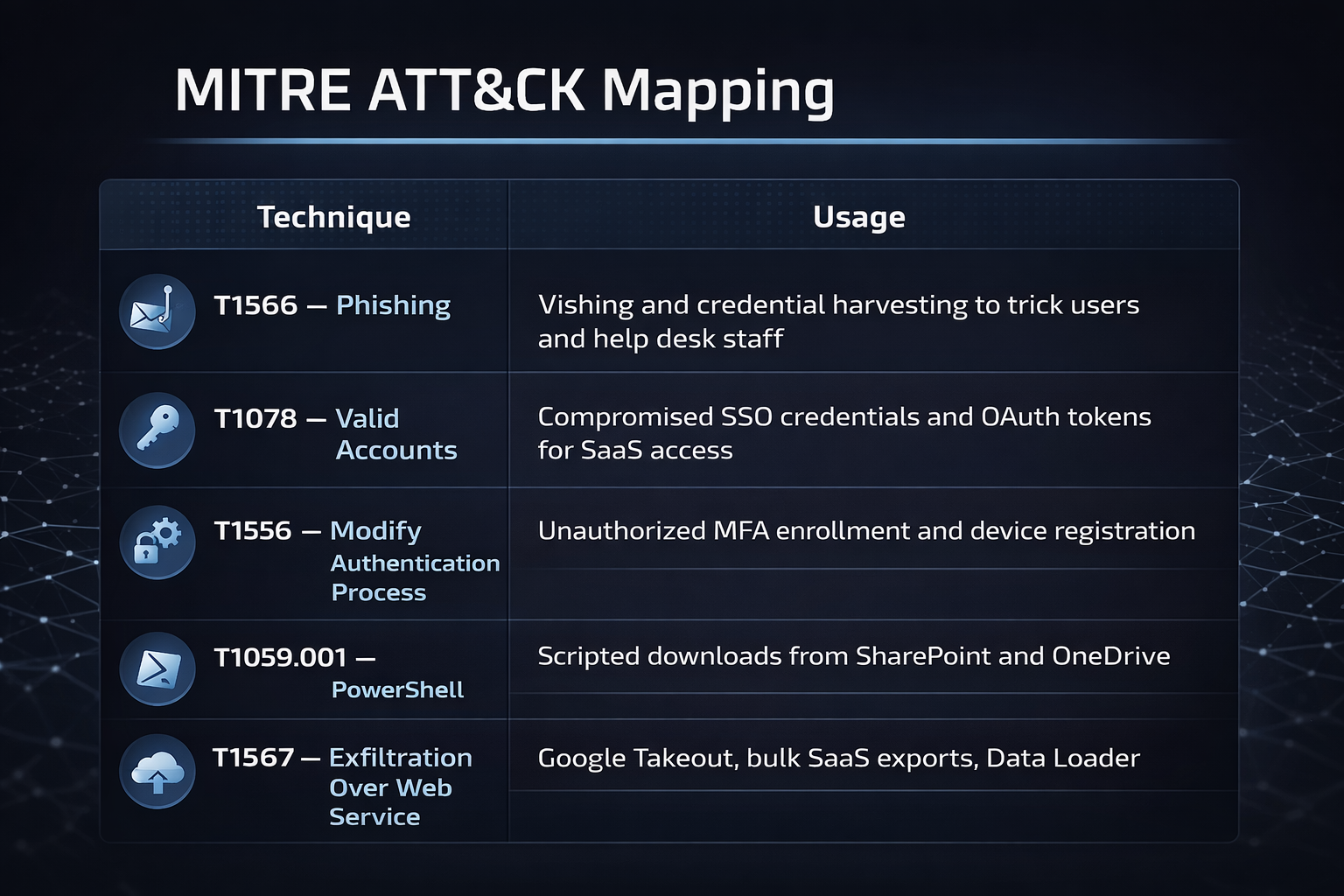
MITRE ATT&CK Mapping
Indicators of Compromise
The Mandiant report references campaign-specific indicators including:
- Network infrastructure — ShinyHunters proxy IPs and VPN/Tor ASNs used for authentication and admin actions
- OAuth applications — ToogleBox / "recall" app authorizations enabling mailbox and config changes
- User-agent strings — WindowsPowerShell / PowerShell user-agent observed during SharePoint/OneDrive downloads
- Export indicators — Google Takeout export job IDs and initiation/completion events
- Credential artifacts — Service account key creation events, long-lived access keys, API tokens
- Mailbox cleanup — Deletion of emails with subjects like "Security method enrolled" or "new sign-in"
Organizations are advised to check their specific IP and ASN reference lists against their environment logs and maintain curated allowlists/blocklists for detection tuning.
Logging Requirements
Mandiant stresses that without proper visibility into identity actions, authorizations, and SaaS export behaviors, detection is effectively impossible — organizations often remain unaware of a compromise until an extortion note arrives.
Critical logging that should be enabled and ingested into SIEM:
- Okta — Authentication events, MFA lifecycle events, administrative identity events
- Entra ID — Auth events, audit logs for MFA changes, Conditional Access policy changes, Named Location changes
- Google Workspace — OAuth authorization logs, Gmail audit logs (including deletion events and subject metadata), Takeout audit logs
- Salesforce — LoginHistory, SetupAuditTrail, ApiEventStream, ReportEventStream, BulkApiResultEvent (requires Event Monitoring license)
- Microsoft 365 — SharePoint/OneDrive FileDownloaded and FileAccessed events with UserAgent context
- DocuSign — Authentication, admin changes, envelope access, API activity
- Atlassian — SSO sign-ins, privilege changes, Confluence export events, API token activity



