Single Bulletproof Hosting IP Behind 83% of Ivanti EPMM Exploitation as Sleeper Shells Target MDM Infrastructure

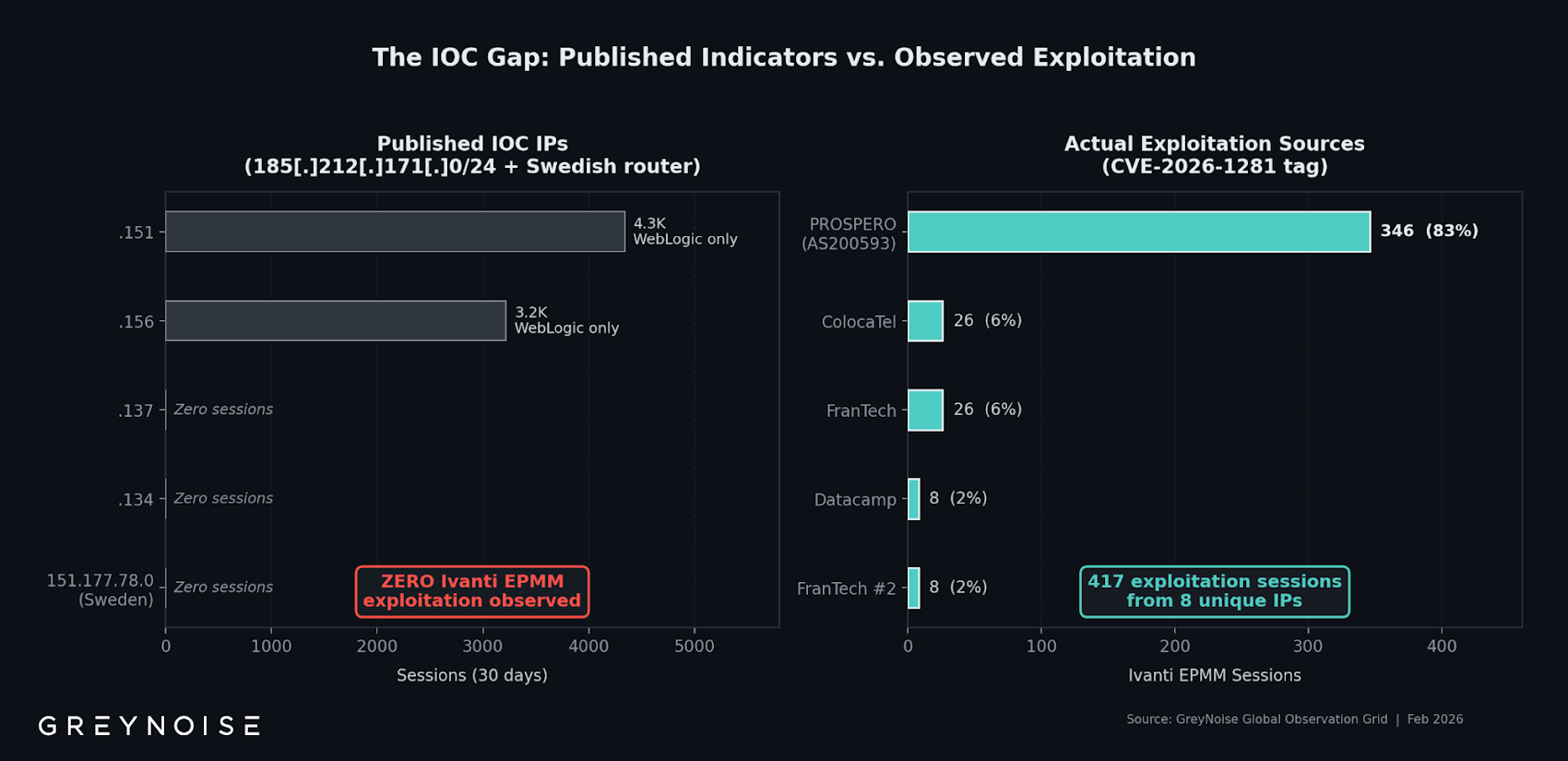
A single IP address on bulletproof hosting infrastructure is responsible for 83% of all exploitation attempts targeting the critical Ivanti Endpoint Manager Mobile (EPMM) vulnerabilities that have already compromised multiple European government agencies.
Threat intelligence firm GreyNoise recorded 417 exploitation sessions from 8 unique source IPs between February 1-9, with 346 sessions — 83% of the total — originating from 193.24.123[.]42 on infrastructure operated by PROSPERO (AS200593).
Targeting CVE-2026-1281
The exploitation targets CVE-2026-1281 (CVSS 9.8), one of two critical EPMM vulnerabilities alongside CVE-2026-1340 that enable unauthenticated remote code execution. Ivanti acknowledged zero-day exploitation of both flaws affecting a "very limited number of customers" before patches were available.
Since disclosure, multiple European agencies have confirmed they were targeted — including the Netherlands' Dutch Data Protection Authority, the Council for the Judiciary, the European Commission, and Finland's Valtori.
Automated Multi-Exploit Tooling
The dominant IP isn't limited to Ivanti. GreyNoise found the same host simultaneously exploiting three unrelated CVEs:
CVE-2026-21962 (Oracle WebLogic) — 2,902 sessions
CVE-2026-24061 (GNU InetUtils telnetd) — 497 sessions
CVE-2025-24799 (GLPI) — 200 sessions
The IP rotates through over 300 unique User-Agent strings spanning Chrome, Firefox, Safari, and multiple operating system variants. This fingerprint diversity combined with concurrent exploitation of four unrelated products is consistent with automated tooling operating at scale.
PROSPERO's Malware Distribution History
PROSPERO is assessed to be linked to the autonomous system Proton66, which has a documented history of distributing both desktop and Android malware including GootLoader, Matanbuchus, SpyNote, Coper (Octo), and SocGholish.
Sleeper Shell Campaign
Separately, Defused Cyber reported a "sleeper shell" campaign deploying dormant in-memory Java class loaders to compromised EPMM instances at the path /mifs/403.jsp. The implants establish persistent access without deploying active payloads — consistent with initial access broker tradecraft where threat actors establish footholds to sell or hand off to ransomware operators later.
GreyNoise confirmed that 85% of exploitation sessions used DNS beaconing via out-of-band application security testing (OAST) callbacks to verify exploitability without deploying malware or exfiltrating data. The operators are cataloging vulnerable targets rather than exploiting them immediately.
Recommendation
Patch EPMM immediately if not already applied. Audit all internet-facing MDM infrastructure for signs of compromise. Review DNS logs for OAST-pattern callbacks indicating exploitation verification. Monitor for the /mifs/403.jsp path on EPMM instances. Block PROSPERO's autonomous system (AS200593) at the network perimeter. EPMM compromise provides access to device management infrastructure for entire organizations — creating a lateral movement platform that bypasses traditional network segmentation.



