SolarWinds Web Help Desk Hit with Six Critical Vulnerabilities Including Multiple RCE Flaws
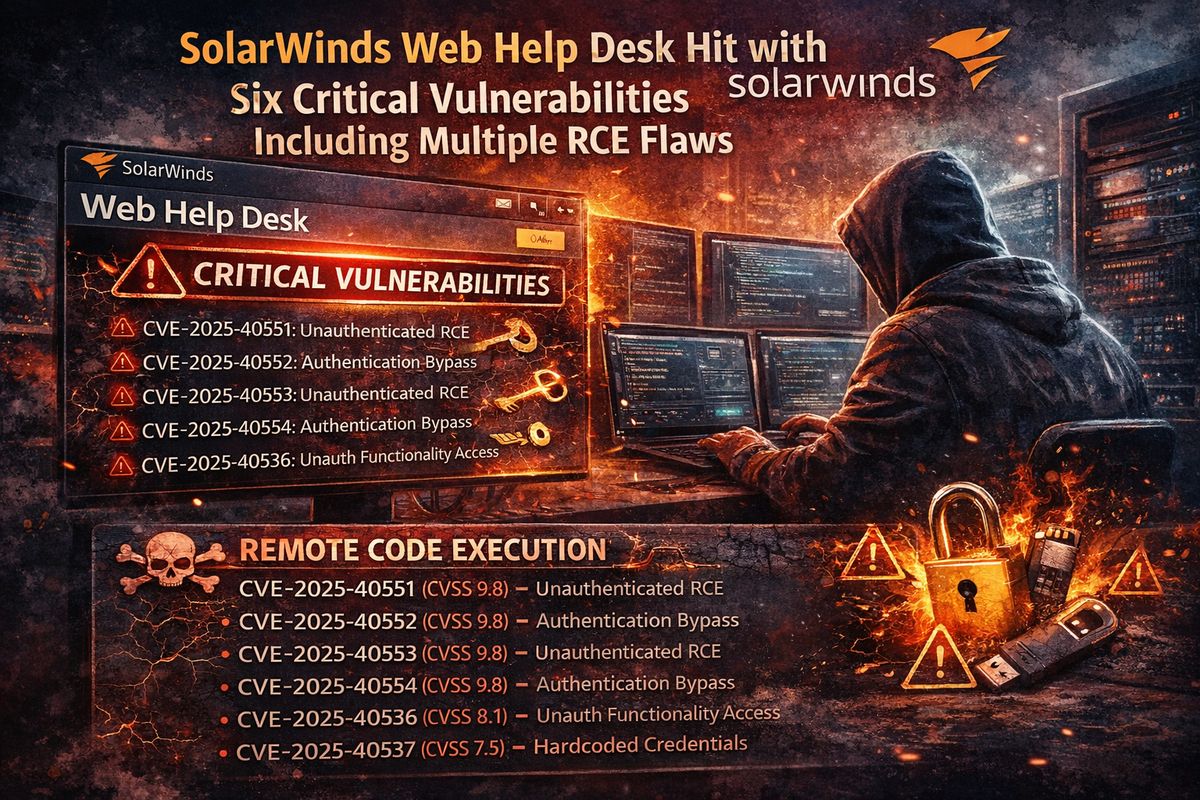
SolarWinds has released an emergency patch for Web Help Desk (WHD), addressing six security vulnerabilities—four rated critical—that could allow unauthenticated attackers to fully compromise host systems.
The flaws, discovered by researchers Jimi Sebree of Horizon3.ai and Piotr Bazydło of watchTowr, include multiple remote code execution vectors, authentication bypasses, and hardcoded credentials.
Critical Vulnerabilities (CVSS 9.8)
CVE-2025-40551 – Deserialization of untrusted data leading to remote code execution. Exploitable without authentication.
CVE-2025-40552 – Authentication bypass allowing attackers to execute protected actions and methods.
CVE-2025-40553 – Second deserialization vulnerability enabling unauthenticated remote code execution.
CVE-2025-40554 – Authentication bypass permitting attackers to invoke specific actions within Web Help Desk.
High Severity Vulnerabilities
CVE-2025-40536 (CVSS 8.1) – Security control bypass allowing unauthenticated access to restricted functionality.
CVE-2025-40537 (CVSS 7.5) – Hardcoded credentials that could grant access to administrative functions under certain conditions.
Why This Matters
SolarWinds products remain high-value targets following the 2020 supply chain compromise that affected thousands of organizations including U.S. government agencies. Web Help Desk is deployed across enterprises for IT service management, making these vulnerabilities particularly dangerous.
The combination of unauthenticated RCE and authentication bypass flaws means attackers can gain full control of WHD servers without any credentials—a worst-case scenario for exposed instances.
Affected Products
- SolarWinds Web Help Desk (all versions prior to 2026.1)
Remediation
SolarWinds has addressed all six CVEs in WHD version 2026.1, released January 28, 2026. Organizations should:
- Update to WHD 2026.1 immediately
- Review Web Help Desk access logs for suspicious activity
- Ensure WHD instances are not exposed to the internet
- Change default admin credentials if not already done
- Create new client accounts rather than using built-in demo accounts in production



