Step Finance Loses $40M in Crypto After Executive Devices Compromised

Step Finance, one of the most widely used DeFi dashboard and analytics platforms on Solana, has disclosed that attackers stole approximately $40 million in digital assets after compromising devices belonging to company executives.
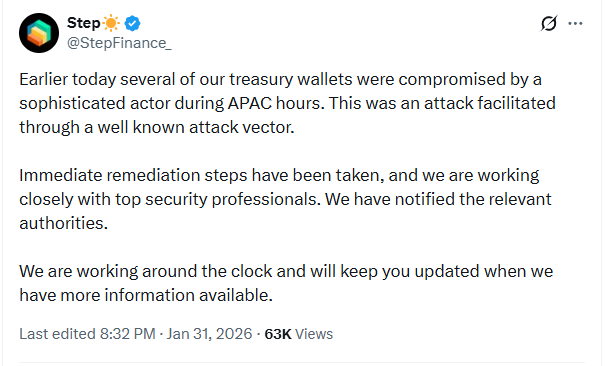
The breach was detected on January 31 during APAC hours. Step Finance described the attacker as a "sophisticated actor" who leveraged "a well-known attack vector" to access multiple treasury wallets. The company has not disclosed specifics about the attack method or attributed the intrusion to any known threat group.
What Happened
Blockchain analytics firm CertiK initially estimated the loss at 261,854 SOL (approximately $28.9 million at the time), but Step Finance's own investigation put the total closer to $40 million.
Recovery efforts have reclaimed roughly $4.7 million so far — $3.7 million in Remora assets and $1 million in other positions — aided by Token22 protections and coordination with partners. The remaining $35+ million is unrecovered.
Step Finance has halted some platform operations while security reinforcement is underway. The company confirmed that Remora Markets, which it owns, is isolated from the incident and that all rTokens remain fully backed 1:1.
What We Don't Know
Step Finance has not disclosed the specific attack vector beyond calling it "well-known," has not identified the threat actors, and has not explained how executive devices were compromised — whether through malware, social engineering, SIM swapping, or another method.
The lack of detail has fueled speculation in the Solana community about a potential insider incident. Those claims remain unsubstantiated, but the company has not directly addressed them either.
User Guidance
Step Finance is advising users not to engage with the $STEP token until the investigation concludes. The company plans to take a snapshot of the pre-exploit state as the basis for a remediation plan for STEP holders.
Context
The $40 million loss represents roughly 10% of the total crypto theft volume for January 2026. CertiK data shows $398 million stolen across the crypto ecosystem in January alone, with only $4.366 million recovered industry-wide. In 2025, 147 confirmed hacks resulted in nearly $2.87 billion in losses.
The incident follows a pattern of executive-targeted attacks in the crypto space, where compromising a small number of high-privilege devices can yield direct access to treasury wallets and signing keys — bypassing the need to exploit smart contracts or protocol-level vulnerabilities entirely.



