Threats
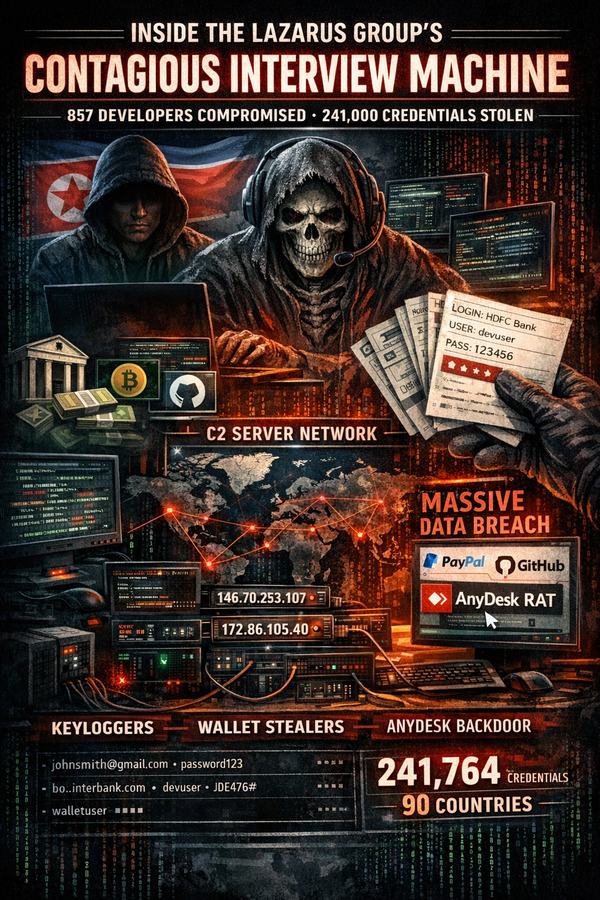
Inside the Lazarus Group's Contagious Interview Machine: 857 Developers Compromised, 241,000 Credentials Stolen
A months-long offensive investigation by Red Asgard's threat research team has produced one of the most detailed public examinations of North Korea's Contagious Interview campaign infrastructure ever published. The findings — spanning four malware families, approximately 20 previously undocumented C2 servers, a novel binary protocol, and unauthenticated