Threat Actors Exploit React2Shell Vulnerability to Deploy Cryptocurrency Miners and Botnets Worldwide
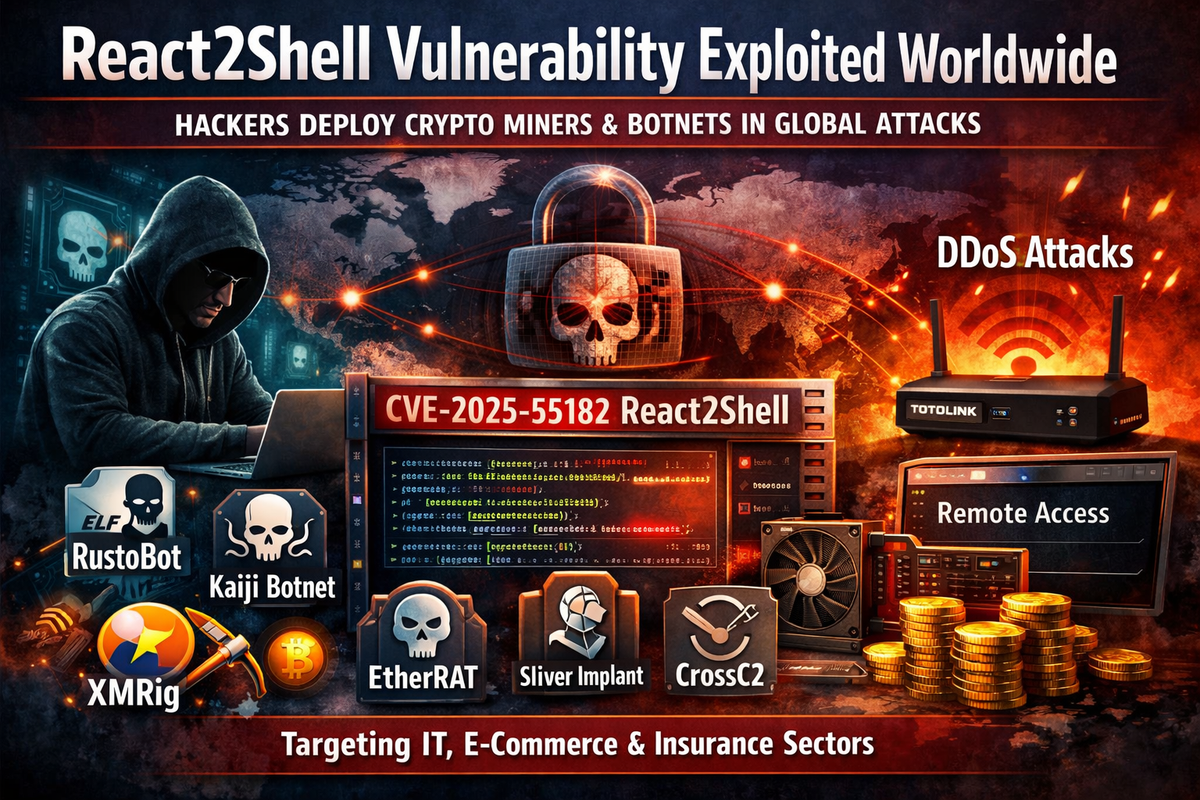
Threat actors are actively exploiting a critical remote code execution vulnerability in React Server Components to compromise systems across multiple industries worldwide, deploying cryptocurrency miners, botnets, and remote access tools, according to research from BI.ZONE Threat Detection and Response.
The vulnerability, tracked as CVE-2025-55182 and commonly referred to as React2Shell, affects the Flight protocol responsible for client-server communication in React Server Components. The flaw stems from insecure deserialization where servers accept client-supplied data without sufficient validation, enabling attackers to achieve remote code execution under specific conditions.
Exploitation Began Shortly After Disclosure
Campaigns exploiting React2Shell were first observed in December 2025, shortly after vulnerability details became publicly available. BI.ZONE detected malicious activity targeting companies in the Russian insurance, e-commerce, and IT sectors leveraging the vulnerability.
The vulnerable packages include react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack versions 19.0 through 19.2.0. Security patches were released in versions 19.0.1, 19.1.2, and 19.2.1, but exploitation continues against unpatched systems.
Diverse Malware Arsenal Deployed
Attackers have deployed a wide range of payloads following successful exploitation, including XMRig cryptocurrency miner, RustoBot botnet, Kaiji botnet, Sliver implant, EtherRAT, CrossC2 for Cobalt Strike, Tactical RMM, and VShell.
In one documented case targeting Russian organizations, attackers exploited the vulnerability inside a container environment and executed chained commands to download an ELF binary identified as RustoBot, a Rust-based botnet primarily associated with attacks on TOTOLINK devices. RustoBot is capable of launching UDP flood, TCP flood, and Raw IP flood DDoS attacks with configurable parameters. The malware also embeds XMRig as a secondary payload to monetize compromised infrastructure.
Following initial infection, attackers executed Base64-encoded shell commands retrieving additional scripts that installed UPX-packed XMRig binaries and established persistence through systemd services and cron jobs.
Kaiji Botnet Replaces System Utilities
Further activity included deployment of the Kaiji botnet's Ares build, which supports SYN, ACK, and UDP flood attacks, WebSocket abuse, command execution, dynamic encrypted configuration files, and extensive persistence mechanisms. Kaiji also replaces system utilities including ls, ps, and netstat to conceal its presence while deploying XMRig for additional monetization.
Attackers later delivered Sliver implants using scripts that handled privilege-aware persistence and aggressively erased forensic traces by clearing shell history and deleting temporary files.
Ethereum Smart Contract Used for C2
One of the more sophisticated payloads observed was EtherRAT, which retrieves its command-and-control address from an Ethereum smart contract before contacting the C2 server to fetch JavaScript payloads. This technique provides resilient infrastructure that is difficult to take down through traditional methods.
Additional campaigns featured DNS-based data exfiltration, where attackers executed reconnaissance commands and tunneled results via DNS queries. This was followed by XMRig installation from GitHub and persistence via systemd services.
Global Targeting Beyond Russia
Outside Russia, React2Shell exploitation has delivered a broader malware ecosystem including CrossC2 for Cobalt Strike, Tactical RMM, VShell, and EtherRAT. These tools enable long-term access, command execution, encrypted C2 communication, and stealthy persistence across multiple sectors and countries.
Recommendations
Organizations using React Server Components should immediately verify they are running patched versions 19.0.1, 19.1.2, or 19.2.1 or later. Given the active exploitation and variety of threat actors leveraging this vulnerability, unpatched systems should be considered at high risk.
Security teams should monitor for indicators of compromise including unexpected systemd services, cron job modifications, and network connections to known malicious infrastructure. Container environments should be audited for signs of exploitation and lateral movement.



