Ukraine and Germany Expose Ransomware Group Members, Russian Organizer Placed on INTERPOL Wanted List

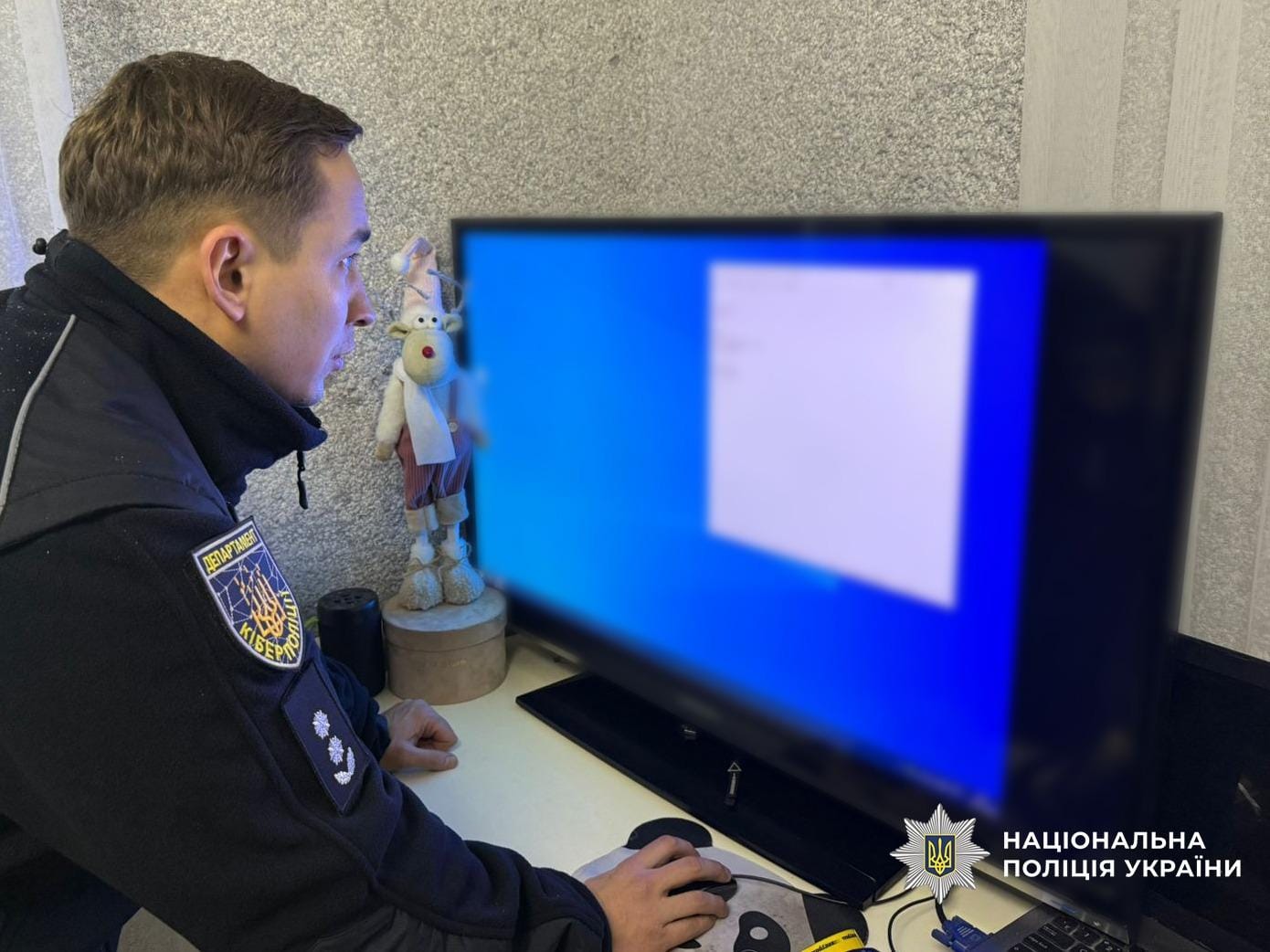
Ukrainian and German law enforcement have identified members of a Russian-affiliated ransomware group responsible for hundreds of millions of euros in damages, with searches conducted in Ukraine and the alleged organizer placed on INTERPOL's international wanted list.
The Operation
Cyber police officers from Ukraine's National Police, working with Germany's Federal Criminal Police (BKA) and Europol, identified two members operating within Ukraine who performed technical roles for the criminal group.
Searches were conducted at residences in the Ivano-Frankivsk and Lviv regions, where authorities seized digital media and cryptocurrency assets as evidence.
Technical Roles
The two suspects specialized as "hash crackers" - individuals who extract account passwords from protected systems using specialized software.
Their attack methodology involved:
- Extracting employee credentials from corporate systems
- Gaining unauthorized access to internal networks
- Escalating privileges on compromised accounts
- Compromising critical systems
- Stealing confidential data
- Deploying ransomware to encrypt systems and demand payment
The Organizer
The joint investigation also identified the alleged organizer - a Russian national suspected of creating and leading the group. At the initiative of Germany's BKA and the Frankfurt Public Prosecutor's Office, he has been declared internationally wanted through INTERPOL.
Foreign law enforcement partners indicate he may also be connected to Conti, one of the most notorious ransomware operations in recent years.

Scale of Damage
According to law enforcement, the group is considered one of the most dangerous cybercriminal operations in recent years. Between 2022 and 2025, members attacked hundreds of organizations across Western countries, causing hundreds of millions of euros in losses.
Primary targets included companies, institutions, and government authorities in economically developed nations.
International Cooperation
The investigation involved law enforcement from Ukraine, Germany, Switzerland, the Netherlands, and the United Kingdom. Ukrainian police had previously conducted searches in Kharkiv related to this group.



