Unit 42 Exposes TGR-STA-1030: State-Aligned Espionage Group Compromised 37 Countries in One Year
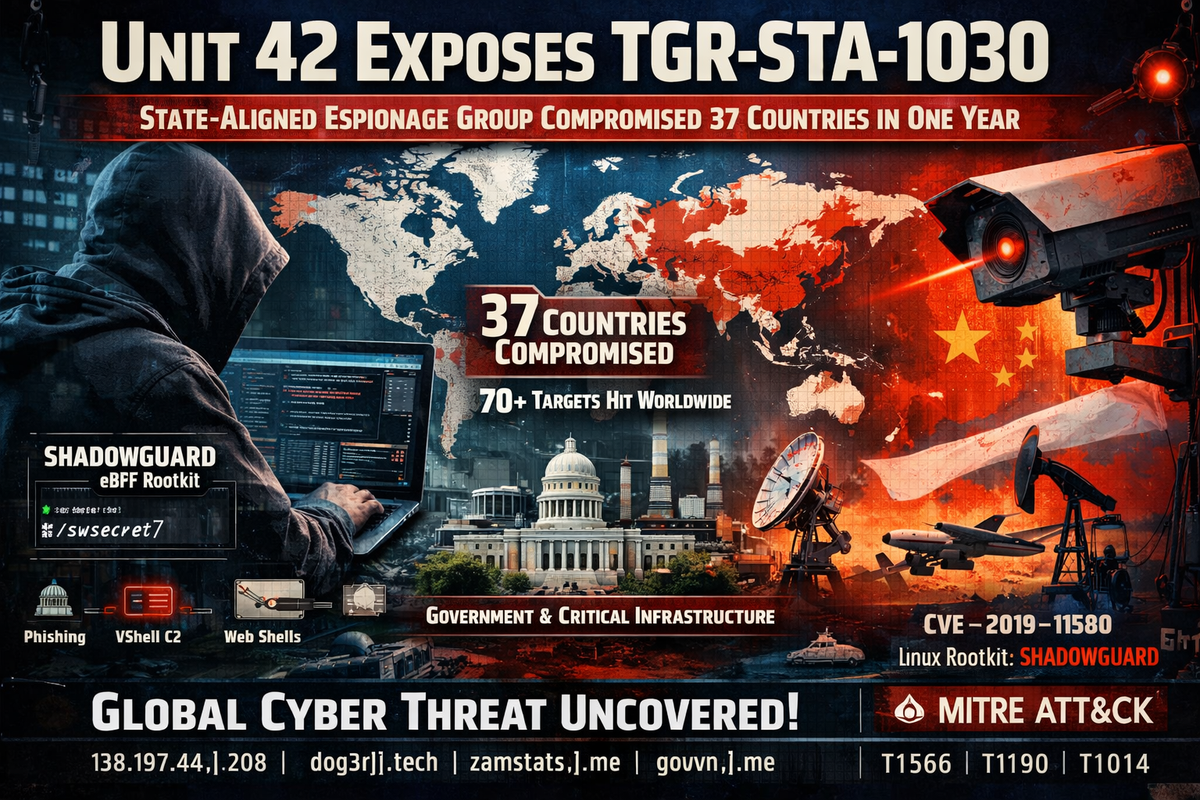
Palo Alto Networks' Unit 42 has published a major investigation into a newly identified cyberespionage group it tracks as TGR-STA-1030, also known as UNC6619. The group — assessed with high confidence to be state-aligned and operating out of Asia — has compromised at least 70 organizations across 37 countries over the past year, targeting government ministries, law enforcement agencies, critical infrastructure and telecommunications providers.
Between November and December 2025 alone, the group conducted active reconnaissance against government infrastructure associated with 155 countries — approximately four out of every five nations on earth.
Unit 42 refers to the group's operations as the "Shadow Campaigns."
Attribution
Unit 42 assesses with high confidence that TGR-STA-1030 is a state-aligned group operating out of Asia, based on frequent use of regional tooling and services, language setting preferences, targeting patterns that align with regional economic and diplomatic interests, upstream connections to infrastructure originating from the region, and operational activity consistently aligning with GMT+8.
On several occasions, the group connected directly to relay and victim-facing infrastructure from IP addresses belonging to AS 9808, an internet service provider in the group's assessed region. One operator was observed using the handle "JackMa" — a possible reference to the Alibaba co-founder.
Initial Access: Phishing and Exploitation
The group's operations began with phishing campaigns targeting European governments in early 2025. Emails used ministry reorganization lures and linked to malicious archives hosted on mega[.]nz, customized with language and naming consistent with the targeted country.
Analysis of one such archive — uploaded by an Estonian government entity — revealed an executable internally named DiaoYu.exe ("diaoyu" translating to "fishing" or "phishing"). The loader employs a dual-stage sandbox evasion guardrail: it requires a minimum screen resolution of 1440 pixels and checks for a companion file (pic1.png) in its execution directory. It then audits the host for a narrow selection of security products — Kaspersky, Avira, Bitdefender, SentinelOne and Symantec — before downloading additional payloads from GitHub that ultimately install a Cobalt Strike beacon.
The group has since shifted toward exploitation for initial access, deploying N-day exploits across a wide range of vulnerabilities including Microsoft Exchange RCE, SAP Solution Manager privilege escalation, D-Link RCE, and Atlassian Crowd authentication bypass (CVE-2019-11580), among others.
Tooling
TGR-STA-1030's tooling has evolved significantly over the past year.
C2 Frameworks: The group transitioned from Cobalt Strike to VShell — a Go-based C2 framework — as its primary tool. It has also leveraged Havoc, SparkRat and Sliver with varying success.
Web Shells: Behinder, Neo-reGeorg and Godzilla are the group's most commonly deployed web shells, used on both external-facing and internal servers for persistence and lateral movement.
Tunneling: GO Simple Tunnel (GOST), Fast Reverse Proxy Server (FRPS) and IOX are used across C2 infrastructure and compromised networks.
ShadowGuard: A New Linux eBPF Rootkit
The most significant technical finding is a previously undocumented Linux kernel rootkit Unit 42 has named ShadowGuard. The tool is an Extended Berkeley Packet Filter (eBPF) rootkit — assessed to be unique to this group — that operates entirely within kernel space, making it exceptionally difficult to detect.
ShadowGuard provides kernel-level process concealment by intercepting system calls, hiding up to 32 processes simultaneously from standard user-space tools like ps aux. It automatically hides any files or directories named "swsecret" and includes an allow-list mechanism to exclude specified processes from its hiding functionality.
The rootkit requires root privileges and eBPF/tracepoint support to operate. Because eBPF programs execute inside the kernel's BPF virtual machine rather than as separate modules, they can manipulate core system functions and audit logs before security monitoring tools see the true data.
Infrastructure
The group employs a multi-tiered infrastructure approach. Victim-facing C2 servers are hosted on legitimate VPS providers in the US, UK and Singapore — jurisdictions chosen to appear legitimate, enable low-latency global connections, and complicate cross-agency law enforcement cooperation.
Traffic is relayed through additional VPS infrastructure via SSH or RDP, then anonymized through residential proxy services (DataImpulse), Tor, and other proxy services. Upstream connections ultimately trace back to AS 9808 in the group's assessed region when operational errors expose direct connections.
Domains registered under .me, .live, .help and .tech TLDs include gouvn[.]me (targeting Francophone government domains), zamstats[.]me (targeting Zambia) and dog3rj[.]tech (targeting European nations).
Global Victimology
The scope of compromise spans every inhabited continent.
Americas: Government entities compromised in Bolivia, Brazil, Mexico, Panama and Venezuela. Brazil's Ministry of Mines and Energy was breached — likely targeting rare earth mineral intelligence. Following Venezuela's Operation Absolute Resolve on January 3, 2026, the group conducted extensive reconnaissance against 140+ government IPs and likely compromised a Venezolana de Industria Tecnológica facility within 24 hours.
Europe: Government entities compromised across Cyprus, Czechia, Germany, Greece, Italy, Poland, Portugal and Serbia. The group initiated connections to over 490 German government IPs in July 2025 and over 600 EU infrastructure IPs in August. Czech government scanning intensified following President Pavel's meeting with the Dalai Lama.
Asia and Oceania: Compromises confirmed in Afghanistan, Bangladesh, India, Indonesia, Japan, Malaysia, Mongolia, Papua New Guinea, Saudi Arabia, Sri Lanka, South Korea, Taiwan, Thailand, Uzbekistan and Vietnam. A major Taiwanese power equipment supplier was breached, providing access to power generation project data. An Indonesian airline was compromised at Soekarno-Hatta International Airport — likely connected to competing aircraft procurement interests.
Africa: Government entities compromised in the Democratic Republic of the Congo, Djibouti, Ethiopia, Namibia, Niger, Nigeria and Zambia. Activity in the DRC and Zambia correlates with mining operations and environmental incidents involving Asian mining firms.
Targeted Sectors
The group's targeting pattern reveals clear intelligence priorities: economic and trade intelligence, rare earth mineral and mining operations, diplomatic relations, law enforcement and border security, immigration data, military and defense logistics, and telecommunications infrastructure.
Five national-level law enforcement and border control entities were compromised, along with three ministries of finance. One nation's parliament and a senior elected official of another country were also breached.
Detection Guidance
Defenders should monitor for unexpected kernel driver installations, eBPF program loading, processes hiding from standard enumeration tools, and files or directories containing "swsecret." Hunt for VShell C2 activity on 5-digit ephemeral TCP ports and Cobalt Strike beacons communicating with the IOC domains listed below.
Organizations running Atlassian Crowd should verify patches for CVE-2019-11580. Edge device operators — particularly those running Fortinet, Ivanti and Palo Alto products — should audit for exploitation attempts matching the group's known vulnerability targets.
MITRE ATT&CK
- T1566.002 — Phishing: Spearphishing Link (mega[.]nz hosted archives)
- T1059.007 — Command and Scripting Interpreter: JavaScript (NodeSnakeRAT implants)
- T1190 — Exploit Public-Facing Application (N-day exploitation)
- T1071.001 — Application Layer Protocol: Web Protocols (VShell, Cobalt Strike C2)
- T1505.003 — Server Software Component: Web Shell (Behinder, Godzilla, Neo-reGeorg)
- T1572 — Protocol Tunneling (GOST, FRPS, IOX)
- T1014 — Rootkit (ShadowGuard eBPF rootkit)
- T1564.001 — Hide Artifacts: Hidden Files and Directories (swsecret concealment)
- T1057 — Process Discovery (process enumeration and PID hiding)
- T1078 — Valid Accounts (compromised government credentials)
Indicators of Compromise
IP Addresses: 138.197.44[.]208, 142.91.105[.]172, 146.190.152[.]219, 157.230.34[.]45, 157.245.194[.]54, 159.65.156[.]200, 159.203.164[.]101, 178.128.60[.]22, 178.128.109[.]37, 188.127.251[.]171, 188.166.210[.]146, 208.85.21[.]30
Domains: abwxjp5[.]me, brackusi0n[.]live, dog3rj[.]tech, emezonhe[.]me, gouvn[.]me, msonline[.]help, pickupweb[.]me, pr0fu5a[.]me, q74vn[.]live, servgate[.]me, zamstats[.]me, zrheblirsy[.]me
Phishing/Downloader Hashes (SHA-256): 66ec547b97072828534d43022d766e06c17fc1cafe47fbd9d1ffc22e2d52a9c0 23ee251df3f9c46661b33061035e9f6291894ebe070497ff9365d6ef2966f7fe
Cobalt Strike Hashes (SHA-256): 5175b1720fe3bc568f7857b72b960260ad3982f41366ce3372c04424396df6fe 358ca77ccc4a979ed3337aad3a8ff7228da8246eebc69e64189f930b325daf6a 293821e049387d48397454d39233a5a67d0ae06d59b7e5474e8ae557b0fc5b06 c876e6c074333d700adf6b4397d9303860de17b01baa27c0fa5135e2692d3d6f b2a6c8382ec37ef15637578c6695cb35138ceab42ce4629b025fa4f04015eaf2 5ddeff4028ec407ffdaa6c503dd4f82fa294799d284b986e1f4181f49d18c9f3 182a427cc9ec22ed22438126a48f1a6cd84bf90fddb6517973bcb0bac58c4231
ShadowGuard Hash (SHA-256): 7808b1e01ea790548b472026ac783c73a033bb90bbe548bf3006abfbcb48c52d
CVE-2019-11580 Exploit Hash (SHA-256): 9ed487498235f289a960a5cc794fa0ad0f9ef5c074860fea650e88c525da0ab4



