VMware ESXi Zero-Day Flaws Were Likely Exploited in the Wild More Than a Year Before Disclosure

Security researchers have uncovered evidence suggesting that threat actors speaking Chinese may have been exploiting serious vulnerabilities in VMware ESXi long before these flaws were publicly disclosed by the vendor.
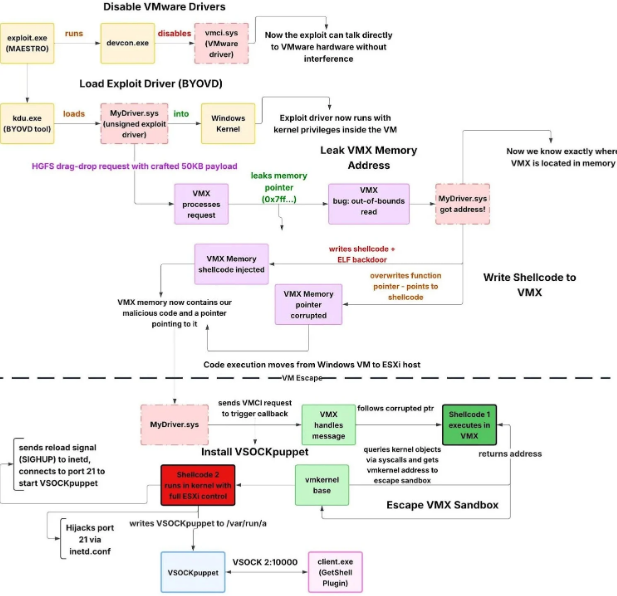
According to a new analysis by cybersecurity firm Huntress, a breach observed in December 2025 began with the compromise of a SonicWall VPN appliance. The attackers then deployed a sophisticated toolkit designed to break out of a virtual machine (VM) and compromise the underlying ESXi hypervisor — the core virtualization layer that controls VM execution.
The toolkit appears to chain together three VMware security flaws that were officially disclosed as zero-days in March 2025. While one of the vulnerabilities had a critical severity score, all three contributed to making the VM escape possible:
- CVE-2025-22226 (CVSS 7.1) – an out-of-bounds read in the Host-Guest File System (HGFS) that could leak memory from the hypervisor process
- CVE-2025-22224 (CVSS 9.3) – a time-of-check/time-of-use (TOCTOU) flaw in the Virtual Machine Communication Interface (VMCI) that could lead to code execution
- CVE-2025-22225 (CVSS 8.2) – an arbitrary write issue that enables sandbox escape to the ESXi kernel
Strong clues from the malicious toolkit suggest it was created well before VMware’s advisory. In some of the build paths inside the exploit binaries, analysts found folders with simplified Chinese text and timestamps indicating development activity more than a year before the vulnerabilities became public. This timing points to a scenario where the exploit toolkit was likely developed as a zero-day weapon that was used covertly before disclosure.
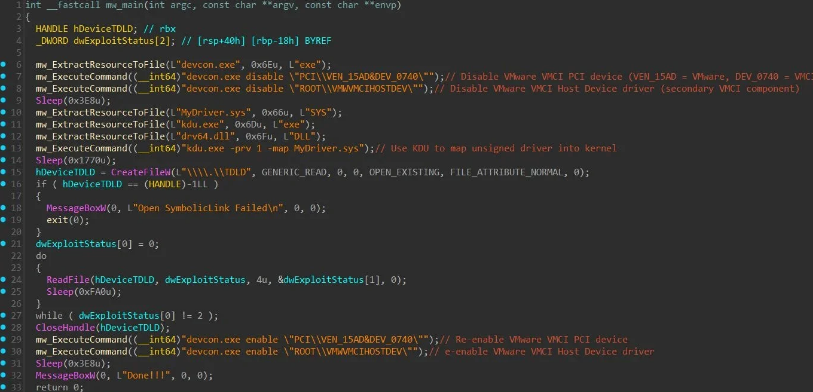
The attackers used the SonicWall VPN compromise to gain elevated privileges inside the victim’s environment — even leveraging a Domain Admin account to spread and execute their tools. From there, they deployed the toolkit that disabled certain VMware drivers, injected unsigned kernel code, and established a covert backdoor into the hypervisor itself.
This type of VM escape is especially dangerous: it breaks the fundamental isolation that virtualization promises, letting threat actors move from a guest VM into full control of the host. Once inside the hypervisor, attackers can access all virtual machines running on that system.
Although researchers have not publicly attributed the campaign to any specific group, the use of simplified Chinese in build artifacts and the sophistication of the toolkit suggest a well-resourced developer operating in a Chinese-speaking region.
Security experts warn that this discovery underscores the need for prompt patching of virtualized infrastructure and careful monitoring of VPN appliances and other entry points that can give attackers an initial foothold.