VoidLink: First Advanced AI-Generated Malware Framework Signals New Era of Threats

Check Point Research has documented what they believe is the first truly advanced malware framework built almost entirely by artificial intelligence, developed by a single individual in under a week.
The discovery of VoidLink marks a significant shift in the threat landscape, demonstrating how AI can enable lone actors to produce sophisticated offensive capabilities that previously required coordinated teams.
Why This Matters
Until now, AI-generated malware has been linked to inexperienced threat actors producing unsophisticated tools. VoidLink is different - it's a mature, modular framework featuring:
- eBPF and LKM rootkits
- Cloud enumeration modules
- Container post-exploitation capabilities
- Flexible command-and-control infrastructure
The malware reached over 88,000 lines of functional code within a week of development starting.
How It Was Built
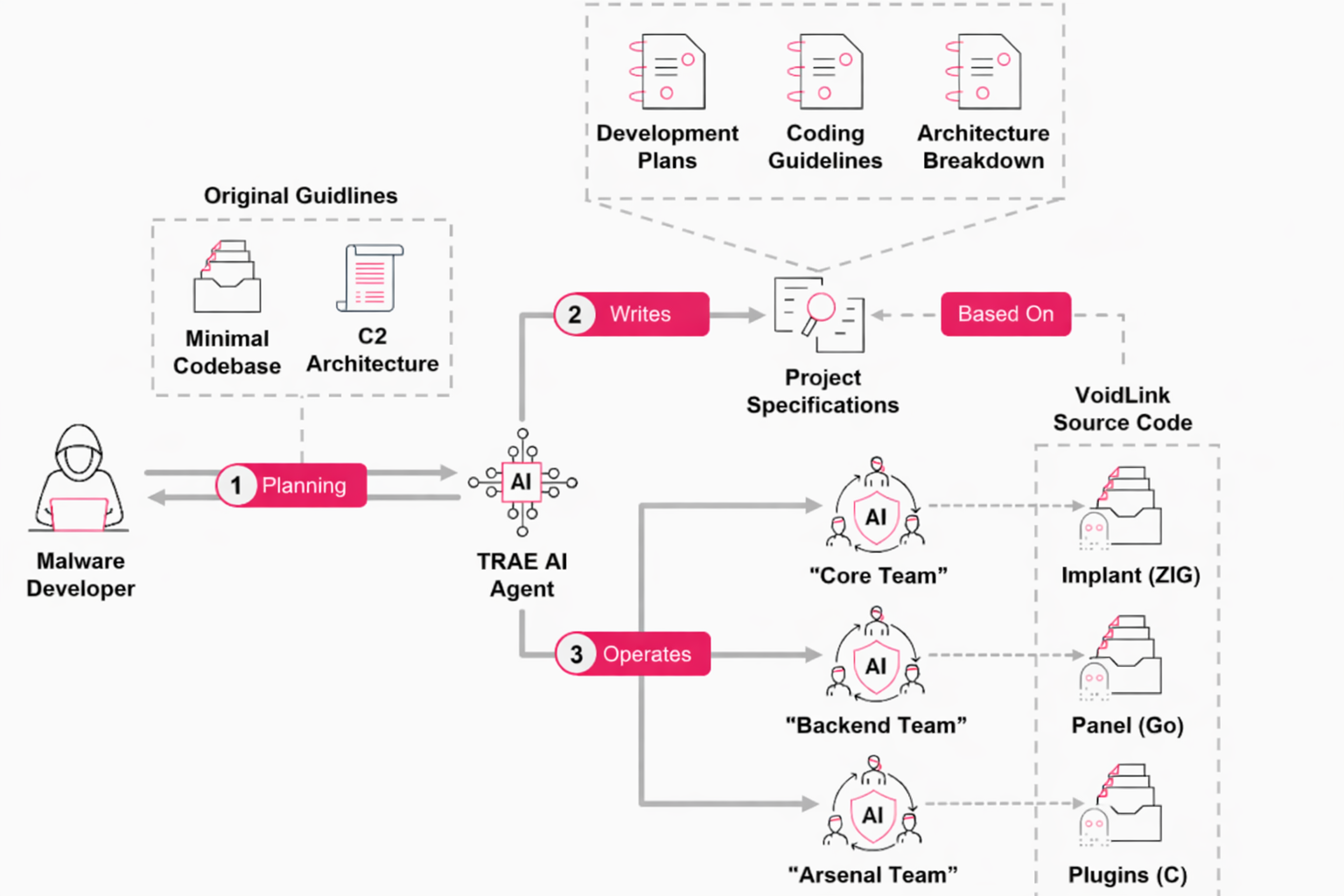
Operational security failures by the developer exposed internal artifacts, revealing the methodology. The developer used TRAE, an AI-centric IDE, following a "Spec Driven Development" approach:
- Defined project requirements and architecture
- Had AI generate a structured development plan across three "teams"
- Created sprint schedules spanning 30 weeks of planned work
- Used AI to implement, iterate, and test the code
The AI produced comprehensive documentation including sprint schedules, coding guidelines, architecture specs, and deployment guides - all in Chinese. The developer then fed these specifications back to the model to generate the actual code.
Rapid Development
What was documented as a 30-week engineering effort was executed in days:
| Date | Milestone |
|---|---|
| Nov 27, 2025 | Project planning began |
| Dec 4, 2025 | 88,000+ lines of functional code |
| Dec 4, 2025 | First VirusTotal submission |
Check Point replicated the workflow using the same tools and confirmed the approach works - the AI generated code matching VoidLink's structure when given the recovered specifications.
The Threat
VoidLink demonstrates that AI in capable hands can:
- Compress months of development into days
- Enable single actors to build team-level sophisticated malware
- Produce stable, stealthy frameworks rivaling nation-state tools
- Normalize high-complexity attacks from low-resource actors
The Unsettling Question
Check Point notes they only discovered VoidLink's AI origins due to the developer's OPSEC failures. Their conclusion: "How many other sophisticated malware frameworks out there were built using AI, but left no artifacts to tell?"



