WorldLeaks Ransomware Group Claims Attack on Nike, Threatens Saturday Data Leak

UPDATE 27/01/2026
Nike has confirmed that it is investigating a potential cybersecurity incident after claims surfaced online that its internal data may have leaked by a cybercrime group. The same group, known for extortion-driven attacks against other companies, previously claimed the Nike cyberattack on its dark web site.
Nike acknowledged the situation of a potential cybersecurity incident, stating, “We always take consumer privacy and data security very seriously. We are investigating a potential cybersecurity incident and are actively assessing the situation.” The company has not yet disclosed whether the cyberattack on Nike involved customer, employee, or partner data.
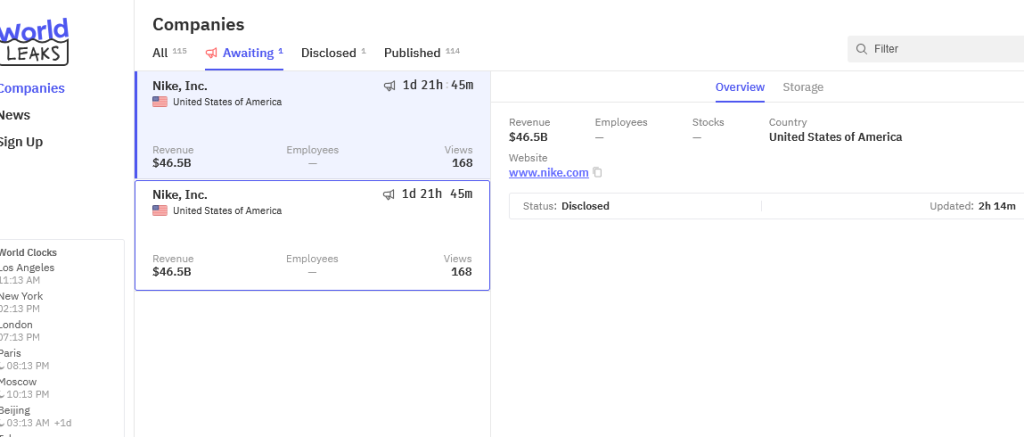
The WorldLeaks ransomware group has claimed responsibility for an attack against Nike, threatening to publish stolen data on Saturday at 6 p.m.
The claim appeared on the group's dark web leak site, where the operation lists victims and announces upcoming data releases. Nike has not issued a public statement confirming or denying the incident, and no technical details about the alleged intrusion have been disclosed.
Unverified Claims
The exact scope and nature of the allegedly stolen data remains unknown. WorldLeaks claims to have exfiltrated a large volume of internal information, though no samples have been publicly released to verify the breach.
Based on previous operations attributed to the group, security analysts believe WorldLeaks typically targets large datasets, sometimes reaching several terabytes.
Potential Attack Vectors
While the intrusion method has not been confirmed, ransomware groups commonly gain initial access through:
- Compromised VPN or remote access credentials
- Exploitation of internet-facing vulnerabilities
- Phishing attacks targeting employees or partners
Possible Data Exposure
If the claims prove legitimate, potentially affected data could include internal corporate documents, customer or partner information, commercial records, and human resources data. Publication of such information could expose employees, customers, and business partners to targeted phishing and fraud attempts.
Nike has not publicly commented on the alleged incident. This story will be updated as more information becomes available.



